Benutzerhandbuch: UFS Explorer Professional Recovery
- 1. Die Grundlagen
- 2. Installation
- 3. Verwendung von UFS Explorer Professional Recovery
- 3.1 Einleitung
- 3.2 Softwareeinstellungen
- 3.3 Operationen
- 4. Rechtliche Hinweise
- 5. Glossar
- 6. Anhang
- 7. Tastenkombinationen
1. Die Grundlagen
1.1 Überblick
UFS Explorer Professional Recovery wurde entwickelt, um selbst die anspruchsvollsten Anforderungen von Datenwiederherstellungsspezialisten zu erfüllen. Mit vielseitigen Datenwiederherstellungstechniken stellt die Software verlorene Dateien von einer Vielzahl von Speichermedien wieder her - von tragbaren Geräten bis zu komplexen RAID-Systemen und virtuellen Maschinen - sowie verschiedenen Dateisystemen. Gleichzeitig gibt es als Antwort auf den reichlich vorhandenen Markt für Betriebssysteme Software-Releases für Windows, Linux und MacOS. Das Programm funktioniert sowohl mit Desktop- als auch mit mobilen, verteilten und zentralisierten, realen und virtuellen Umgebungen. Das Dienstprogramm soll eine bemerkenswerte Wiederherstellungsleistung bei Datenverlusten jeglicher Komplexität bieten - von der einfachen Löschung von Dateien bis zur Datenwiederherstellung nach der vollständigen Zerstörung eines Dateisystems.
Mit einer Fülle von Tools und Funktionen in einer effizienten Software wird diese Anwendung zu einem unersetzlichen Assistenten von Spezialisten auf dem Gebiet der Datenwiederherstellung.
1.2 Spezifikationen und Anforderungen
Unterstützte Host-Betriebssysteme:
- Microsoft Windows ®: ab Windows ® XP mit Service Pack 3 und höher;
- Apple macOS: alle Versionen ab 10.15;
- Linux: Debian Linux 6.0 (oder kompatibel) und höher.
Minimale Konfiguration:
- Jedes der unterstützten Betriebssysteme
- Mindestens 20 MB freier Speicherplatz auf der Festplatte für ausführbare Softwaredateien
- Mindestens 1 GB RAM
- Die Linux-Softwareversion kann von den meisten modernen Linux Live-CDs ausgeführt werden
Empfohlene Konfiguration:
- 64-Bit-Version eines der unterstützten Betriebssysteme
- Über 1 GB freier Speicherplatz auf der Festplatte für das Programm und temporäre Dateien
- Mindestens 4 GB RAM und CPU mit 4 logischen Kernen für parallele Datenverarbeitung
- Standard-Webbrowser
Unterstützte Host-Computerarchitekturen:
- Intel Architektur, 32-Bit (IA-32, x86) - für alle Betriebssysteme;
- AMD64 (x86-64) - für alle Betriebssysteme.
Dateisysteme, die für die Wiederherstellung unterstützt werden:
- NTFS: Vollständige Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, RAID-Wiederherstellung, Wiederherstellung gelöschter Dateien, Wiederherstellung nach Formatierung und Wiederherstellung nach Beschädigung des Dateisystems, Unterstützung von Volumes mit aktivierter Deduplizierung.
- FAT / FAT32: Volle Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, Wiederherstellung gelöschter Dateien, Wiederherstellung nach Format und Wiederherstellung nach Beschädigung des Dateisystems.
- ReFS / ReFS3: Vollständige Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, Wiederherstellung gelöschter Dateien, Wiederherstellung nach Format und Wiederherstellung nach Beschädigung des Dateisystems, Unterstützung von Volumes mit aktivierter Deduplizierung.
- SGI XFS: Vollständige Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, RAID-Wiederherstellung, Wiederherstellung gelöschter Dateien, Wiederherstellung nach Format, Wiederherstellung nach Beschädigung des Dateisystems; Unterstützung von NAS-Geräten und benutzerdefinierten Servern.
- Apple HFS +: Vollständige Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, RAID-Wiederherstellung, Wiederherstellung gelöschter Dateien und Wiederherstellung nach Beschädigung des Dateisystems.
- Apple APFS: Vollständige Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, RAID-Wiederherstellung, Wiederherstellung gelöschter Dateien und Wiederherstellung nach Beschädigung des Dateisystems.
- Linux JFS (JFS2): Vollständige Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, RAID-Wiederherstellung, Wiederherstellung gelöschter Dateien, Wiederherstellung nach Formatierung und Wiederherstellung nach Beschädigung des Dateisystems.
- Ext2-Ext4: Vollständige Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, RAID-Wiederherstellung, Wiederherstellung gelöschter Dateien, Wiederherstellung nach Beschädigung des Dateisystems; Unterstützung von NAS- und benutzerdefinierten Servern.
- ReiserFS: Vollständige Unterstützung: Datenzugriff, Suche nach verlorenen Partitionen, RAID-Wiederherstellung, Wiederherstellung gelöschter Dateien, Wiederherstellung nach Formatierung und Wiederherstellung nach Beschädigung des Dateisystems.
- UFS / UFS2, Adaptec UFS: Datenzugriff, Suche nach verlorenen Partitionen, RAID-Wiederherstellung für Little-Endian- und Big-Endian-Varianten; Wiederherstellung nach Beschädigung des Dateisystems, sehr eingeschränkte Unterstützung für die Wiederherstellung gelöschter Dateien.
- Sun ZFS: Datenzugriff und Unterstützung der Datenwiederherstellung durch einfaches und stripe ZPOOL, eingeschränkte Unterstützung für die Wiederherstellung verlorener Daten. Unterstützung von RAID-Z (RAID-Z2, RAID-Z3).
- Btrfs: Datenzugriff und RAID-Wiederherstellung; Unterstützung von harware RAID, Madadm RAID und Btrfs-RAID.
- Novell NWFS: Nur Datenzugriff und RAID-Wiederherstellung (Kopieren von Dateien und Ordnern aus dem NWFS-Dateisystem).
- Novell NSS: Nur Datenzugriff und RAID-Wiederherstellung (Kopieren von Dateien und Ordnern aus Novel Storage Services).
- HFS: Nur Datenzugriff (Kopieren von Dateien und Ordnern aus dem HFS-Dateisystem).
- VMware VMFS: Unterstützung für RAID-Wiederherstellung, Datenzugriff, sehr eingeschränkte Unterstützung für die Wiederherstellung virtueller Festplatten.
RAID-Unterstützung:
- Unterstützt werden die gängigsten Standard-RAID-Muster für RAID0, RAID 1E, RAID 3, RAID 5, RAID 6, RAID 7 usw.
- RAID-on-RAID-Unterstützung: RAID 10, RAID 50, RAID 60, RAID 50E usw.
- Unterstützung benutzerdefinierter RAID-Layouts über RAID Definition Language oder Runtime VIM.
- Unterstützung von Drobo BeyondRAID und Synology HybridRAID.
- Automatische Rekonstruktion übergreifender Volumes: mdadm, LVM, Apple Software RAID, Core-Speicher, Intel Matrix, Windows Dynamic-Festplatten, MS-Speicherplätze
1.3 Eigenschaften
- Arbeiten Sie mit Geräten, die bestimmte Speichertechnologien implementieren
- Entschlüsselung verschlüsselter Datenträger
- Datenwiederherstellung von RAID- und RAID-basierten Geräten
- Flexibler RAID Builder mit integriertem Script-Handler
- Unterstützung von Festplatten-Images und virtuellen Festplatten
- Automatisches Zusammenfügen übergreifender Volumes
- Datenkonsistenzanalyse und Fehlerkorrektur
- Sofortige Bewertung des Dateisystemstatus
- Sofortiger Zugriff auf Daten konsistenter Dateisysteme
- Automatische Erkennung und manuelle Definition verlorener Partitionen
- Filterung der Wiederherstellungsergebnisse nach benutzerdefinierten Kriterien
- Speichern der Scanergebnisse für weitere Referenzen
- Vor-Ort-Erstellung eines Disk-Images
Installation
2.1 Einrichtung
Die Software-Download-Seite befindet sich unter ufsexplorer.com/ufs-explorer-professional-recovery. Diese Seite enthält auch Verweise auf die Informationen zu Software-Updates, technische Details einschließlich Programmspezifikationen.
Um eine neue Kopie der Software zu installieren oder das Programm zu aktualisieren, sollten Sie die Schritte der Neuinstallation ausführen. Im Falle eines Updates von einer älteren Softwareversion können Sie die ältere Software nicht entfernen. Ein Rollback auf die vorherige Softwareversion erfordert jedoch die Deinstallation der neueren Version. Andere Editionen von UFS Explorer können zusammen mit UFS Explorer Professional Recovery installiert werden.
Für Windows Benutzer
Sie können die Software unter Windows XP mit Service Pack 3 und allen späteren Versionen des Windows-Betriebssystems installieren. Es ist auch möglich, die Software mit älteren Windows-Versionen ab Windows NT 4 mit Service Pack 6 auszuführen, während die Software-Installation unter Windows 95/98 / МЕ überhaupt nicht unterstützt wird. Um die Software zu installieren, laden Sie einfach die ausführbare Datei des Software-Installationsprogramms herunter und führen Sie sie aus.
Achtung: Laden oder installieren Sie niemals die Software auf dem Laufwerk, auf dem sich die verlorenen Daten befinden, die Sie wiederherstellen möchten. Dies kann zu dauerhaftem Schaden oder Verlust führen. Wenn die Daten von einer Nicht-Systempartition verloren gingen, wird empfohlen, die Software auf der Systempartition herunterzuladen und zu installieren. Wenn die Daten aus der Systempartition verloren gingen, wird empfohlen, den Computer sofort herunterzufahren und ihn mit der UFS Explorer-CD für Sicherung und Notfallwiederherstellung zu starten .
Nachdem Sie den Installationsvorgang gestartet haben, werden Sie aufgefordert, die Sprache der Benutzeroberfläche auszuwählen, die als Sprache des Software-Installationsprogramms und des Benutzerhandbuchs verwendet wird. Wenn die Software von einer früheren Version aktualisiert wird, wählt das Installationsprogramm automatisch die vorherigen Spracheinstellungen aus. Danach zeigt Ihnen das Installationsprogramm die Endbenutzer-Lizenzvereinbarung (EULA) zur Annahme. Sie können den Installationsvorgang erst fortsetzen, wenn der EULA akzeptiert wird. Im nächsten Schritt fragt die Software nach dem Zielordner, in den die Anwendung installiert werden soll. Bei einem Software-Update von einer früheren Version wird der Ordner der vorherigen Software-Version standardmäßig als Installationsordner festgelegt.
Dann fordert das Installationsprogramm zur Eingabe des Namens der Produktgruppe im Startmenü auf (der Standardname ist "Data Recovery"). Zu diesem Zeitpunkt sammelt das Installationsprogramm alle erforderlichen Informationen und startet den Installationsvorgang. Nach Abschluss des Vorgangs können Sie die Software im letzten Fenster des Software-Installationsassistenten ausführen. Sie können die Software auch über ihre Verknüpfung im Startmenü ausführen ("Alle Programme", dann die Softwaregruppe (der Standardname ist "Data Recovery").
Für macOS-Benutzer
Laden Sie die komprimierte DMG-Bilddatei von der Software-Website herunter und öffnen Sie sie mit dem Finder. Optional können Sie die Software in den Ordner "Programme" kopieren.
Achtung: Laden oder installieren Sie niemals die Software auf dem Laufwerk, auf dem sich die verlorenen Daten befinden, die Sie wiederherstellen möchten. Dies kann zu dauerhaftem Schaden oder Verlust führen. Wenn die Daten von einer Nicht-Systempartition verloren gingen, wird empfohlen, die Software auf der Systempartition herunterzuladen und zu installieren. Wenn die Daten aus der Systempartition verloren gingen, wird empfohlen, den Computer sofort herunterzufahren und ihn mit der UFS Explorer-CD für Sicherung und Notfallwiederherstellung zu starten .
Für Linux-Benutzer
Laden Sie das Software-Binärarchiv von der Website herunter (z. B. in den Ordner "Downloads") und extrahieren Sie den Inhalt. Öffnen Sie den Ordner in der Terminalanwendung und öffnen Sie den Ordner mit den Binärdateien mit dem Befehl "cd" (z. B. "cd ~/Downloads"). Führen Sie das "install" -Skript als lokaler Administrator aus (z. B. "sudo ./*.install" oder "su root -c ./*.install", dabei ist "* .install" der Name der Installationsdatei – "ufs-explorer-pro.install" für UFS Explorer Professional Recovery).
Achtung: Laden oder installieren Sie niemals die Software auf dem Laufwerk, auf dem sich die verlorenen Daten befinden, die Sie wiederherstellen möchten. Dies kann zu dauerhaftem Schaden oder Verlust führen. Wenn die Daten von einer Nicht-Systempartition verloren gingen, wird empfohlen, die Software auf der Systempartition herunterzuladen und zu installieren. Wenn die Daten aus der Systempartition verloren gingen, wird empfohlen, den Computer sofort herunterzufahren und ihn mit der UFS Explorer-CD für Sicherung und Notfallwiederherstellung zu starten .
Um die Software zu starten, können Sie eine Verknüpfung im Hauptmenü des Window Managers (unter "Systemprogramme") verwenden. Wenn Sie die Software als lokaler Administrator ausführen, geben Sie den Befehl zum Starten der Anwendung ein.
In GNOME:
Drücken Sie Alt + F2, um den Dialog "Anwendung starten" aufzurufen.
Geben Sie "bash -c "xhost +local: && sudo \"/usr/lib/ufs-explorer/ufs-explorer-pro\""" ein.
Im Terminal:
Geben Sie "sudo /usr/lib/ufs-explorer/ufs-explorer-pro" oder "su root -c /usr/lib/ufs-explorer/ufs-explorer-pro" ein.
2.2 Aktivierung
Die Aktivierung des Programms bedeutet den Erwerb einer Lizenz für die vollständige Softwareversion und deren Registrierung. Weitere Informationen zum Unterschied zwischen der Test- / Evaluierungsversion und der vollständigen Version finden Sie im Abschnitt 4.2 Lizenzinformationen. Je nach Einsatzzweck der Software können Sie zwischen zwei Lizenztypen wählen: Es stehen Corporate- und Commercial-Lizenzen zur Verfügung, die jeweils besondere Bedingungen für die Produktnutzung haben. Wenn Sie eine Lizenz erworben haben, erhalten Sie eine Folge von Symbolen, die an die im Kaufformular angegebene E-Mail-Adresse gesendet wird.
Danach sollten Sie die Anwendung ausführen (falls sie noch nicht gestartet wurde) und auf die Schaltfläche "Software-Aktivierung und Lizenz" in der oberen rechten Ecke der Benutzeroberfläche klicken
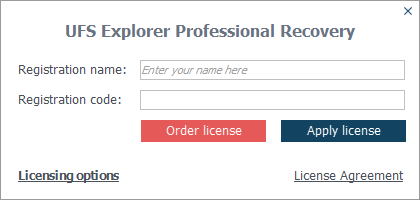
Fügen Sie die ermittelte Folge von Symbolen in das Feld "Registrierungscode" ein und füllen Sie das Feld "Registrierungsname" aus, das mit dem Namen übereinstimmt, der im Zahlungsbeleg als Käufer angegeben ist.
Wenn die gültigen Daten bereitgestellt werden, sollte die Software in den "Registered" -Modus wechseln und die Testeinschränkungen sofort entfernen.
Wenn Sie Probleme mit der Software-Aktivierung haben:
- Stellen Sie sicher, dass Sie die richtige Softwareversion und -edition verwenden.
- sicherstellen, dass die Betriebssystemplattform für die Registrierung gültig ist (verschiedene Betriebssystemplattformen erfordern unterschiedliche Softwarelizenzen);
- Stellen Sie sicher, dass der Registrierungscode wie oben beschrieben kopiert wird
2.3 Aktualisierungen
Das Programm selbst informiert Sie möglicherweise über die Verfügbarkeit einer aktualisierten Version, die heruntergeladen und installiert wird, nachdem Sie auf die Schaltfläche "Installieren" geklickt haben. Sie können auch die Website sysdevlabs.com/de/store aufrufen, das aktualisierte Installationspaket der erforderlichen Software herunterladen und es einfach wie im Abschnitt "Setup" beschrieben ausführen. Sie müssen den Registrierungscode nicht erneut eingeben, wenn Sie einen haben, da sich die Anwendung daran erinnert. Wenn Ihre Softwareversion auf dem neuesten Stand ist, zeigt der Installationsmanager die entsprechende Meldung an.
2.4 Deinstallation
Falls die Software nicht mehr benötigt ist und Sie bereit sind, sie zu deinstallieren, führen Sie die folgenden Schritte aus.
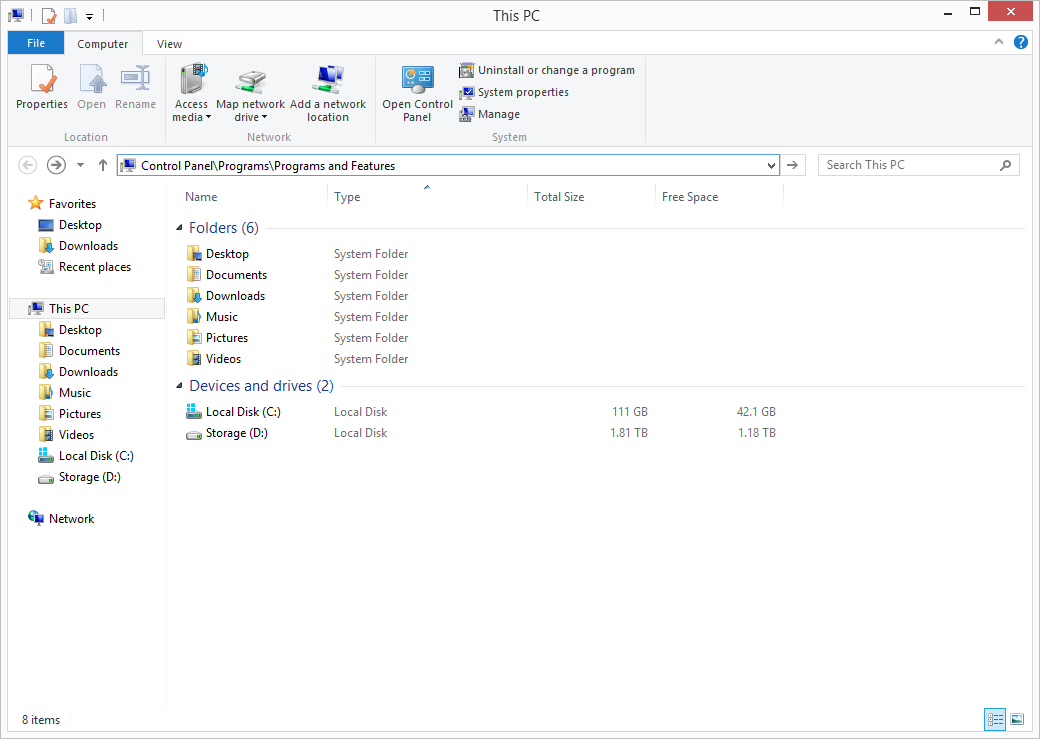
2.4.1 Für Windows
Windows-Benutzer können die Software mithilfe der Standardfunktion für Deinstallation entfernen. Öffnen Sie dazu die Systemsteuerung, gehen Sie zur Kategorie "Programme" und wählen Sie "Programme und Funktionen". Alternativ können Sie Explorer öffnen und "Systemsteuerung\Programme\Programme und Features" in der Adressleiste eingeben. Der Name der zu entfernenden Software lautet "UFS Explorer Professional Recovery".
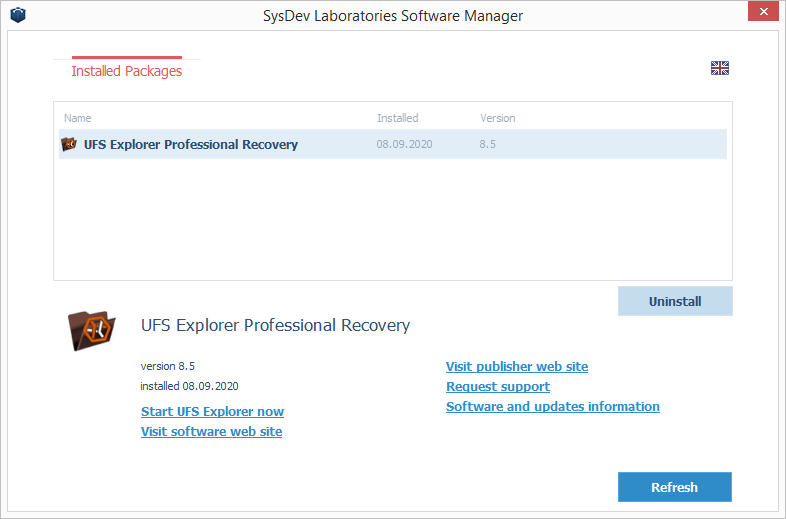
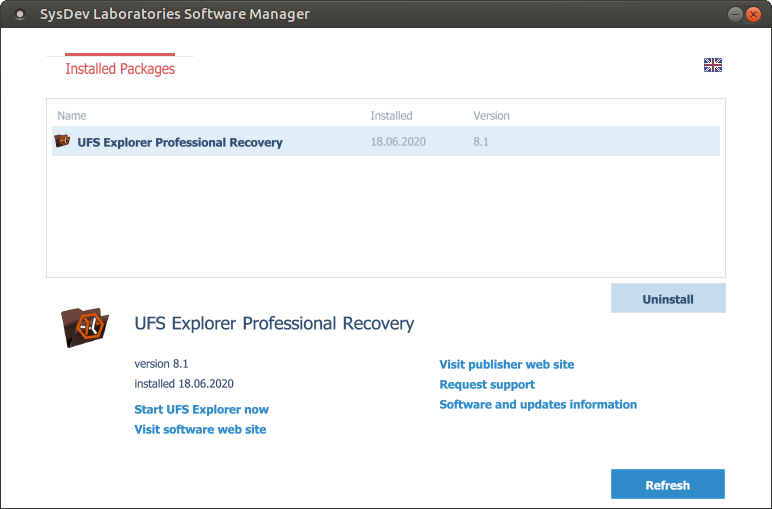
Eine weitere Möglichkeit, die Software zu deinstallieren, ist die Verwendung von "Software Packages Management". Um es zu starten, öffnen Sie das Startmenü, gehen Sie zu "Alle Programme" und wählen Sie die Softwaregruppe (der Standardname ist "SysDev Laboratories"). Führen Sie das Programm mithilfe seiner Verknüpfung aus und deinstallieren Sie die erforderliche Anwendung.
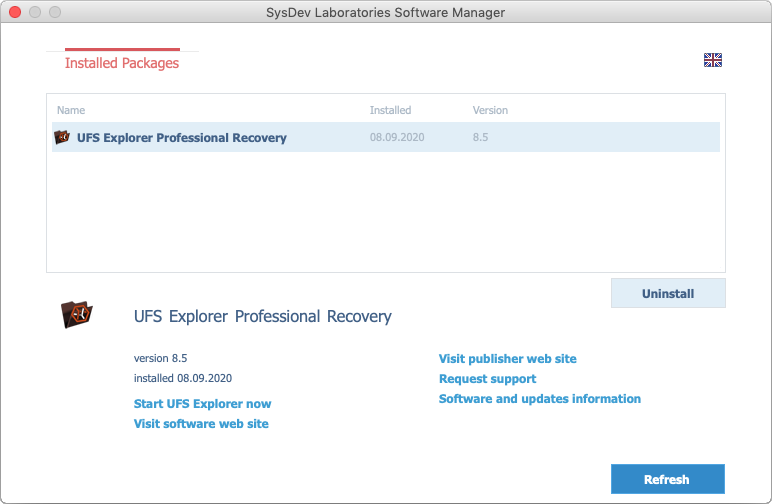
2.4.2 Für macOS
Die Benutzer von macOS können die Software mithilfe von "SDL Software Manager" löschen. Um den auszuführen, öffnen Sie den Finder, gehen Sie zum Ordner "Programme" (die Hotkeys "⇧Shift + ⌘ Cmd + A") und finden Sie "SDL Software Manager". Führen Sie das Programm aus und deinstallieren Sie die erforderliche Anwendung.
Eine andere Möglichkeit, die Software zu deinstallieren, besteht darin, den Finder zu öffnen, sie im Ordner "Programme" zu suchen und in den Papierkorb zu ziehen oder die Option "In den Papierkorb legen" auszuwählen.
2.4.3 Für Linux
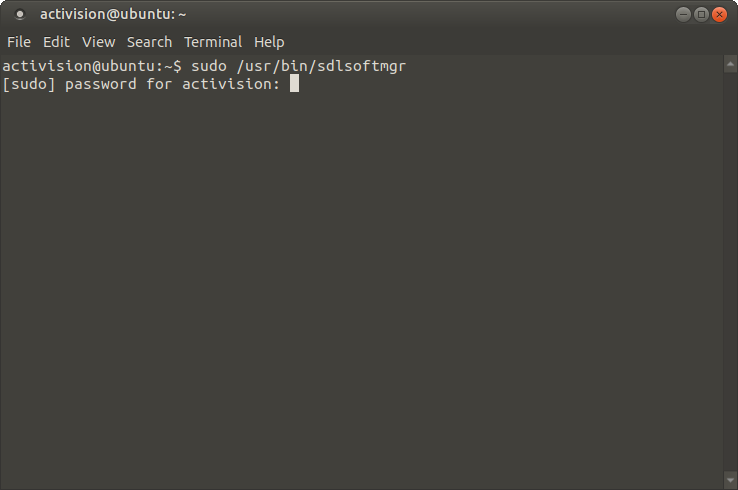
Linux-Benutzer können die Software mithilfe von SDL Software Manager entfernen. Führen Sie einfach das Programm als Administrator aus und deinstallieren Sie die erforderliche Anwendung.
Öffnen Sie dazu das Terminal und geben Sie "sudo /usr/bin/sdlsoftmgr" oder "su root -c /usr/bin/sdlsoftmgr").
3. Verwendung von UFS Explorer Professional Recovery
3.1 Einleitung
Wie bereits in den Abschnitten 1.1 Übersicht und 1.3 Funktionen erwähnt, handelt es sich bei dieser Anwendung um ein professionelles Werkzeug, das von Spezialisten im Bereich Datenwiederherstellung zum Wiederherstellen von Daten verwendet werden soll, die durch versehentliches Löschen, Formatieren und Beschädigen des Dateisystems nach Hardware oder Software verloren gegangen sind Ausfälle usw. Die Software enthält Instrumente zur Datenanalyse und deren manuelle Modifikation, was bedeutet, dass falsche Aktionen, die während der Verwendung der Software ausgeführt werden, zu einem dauerhaften Datenverlust führen können. In diesem Abschnitt werden die Besonderheiten der Softwarenutzung beschrieben und anhand von Beispielen veranschaulicht. Wenn Sie Fragen zur Implementierung bestimmter Verfahren haben, prüfen Sie im Anhang, ob die Frage dort bereits beantwortet wurde.
3.2 Softwareeinstellungen
Gleich nach dem Start kann das Programm mit den optimalen Standardeinstellungen verwendet werden. Der Benutzer kann diese Einstellungen jedoch für eine effizientere Softwareausnutzung in der Registerkarte "Einstellungen" ändern, die über die Schaltfläche "Einstellungen" in der oberen rechten Ecke der Benutzeroberfläche geöffnet wird.
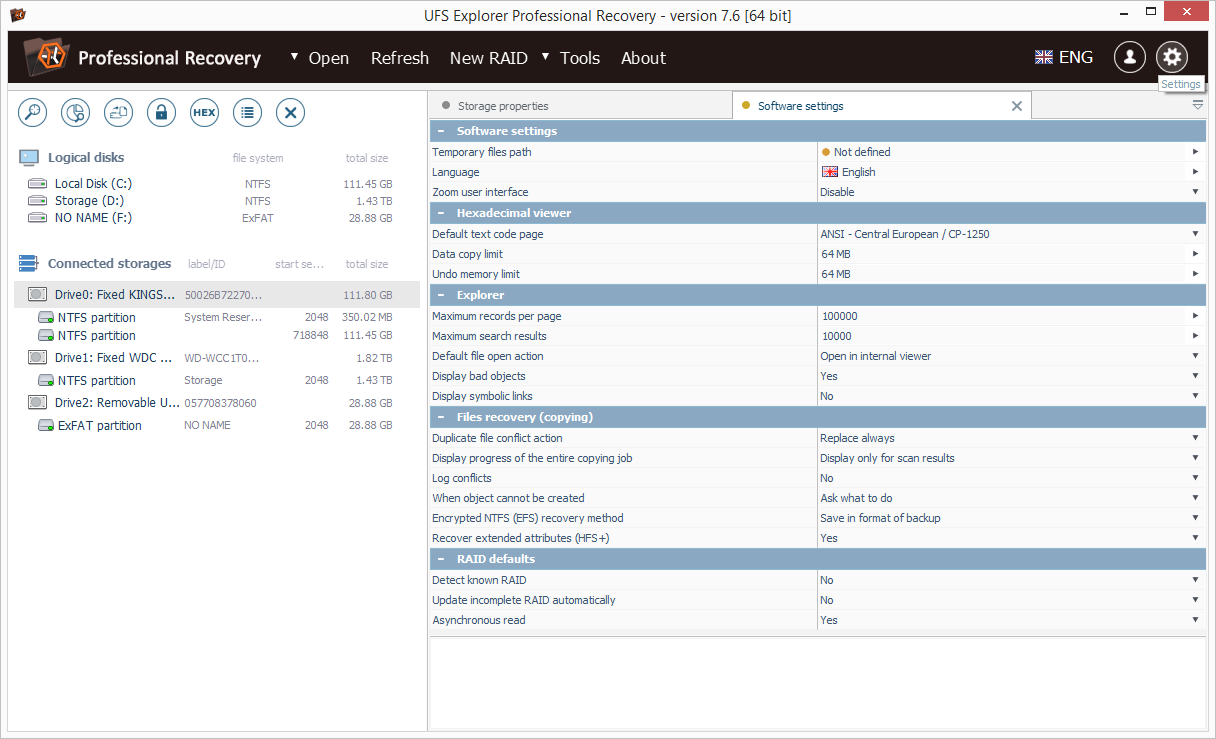
Jeder Wert kann durch Drücken der Schaltfläche "Wert ändern" daneben geändert werden. Alle definierten Einstellungen werden im entsprechenden Benutzerprofilordner in einer speziellen "ufsx" -Datei gespeichert. Die Software speichert keine Daten in der Registrierung des Betriebssystems oder in Konfigurationsdateien (außer Informationen zur Deinstallation (falls zutreffend)).
3.2.1 Pfad der temporären Dateien
Diese Einstellung definiert den Zielordner für das "Ansicht" -Tool des Explorers. Die Software speichert alle temporären Dateien in diesem Ordner. Weitere Informationen finden Sie in der Beschreibung des Explorers. Die Änderungen werden sofort übernommen.
3.2.2 Sprache
Diese Einstellung ermöglicht das Ändern der Sprache der Benutzeroberfläche. Damit die Änderung wirksam wird, muss die Software neu gestartet werden.
3.2.3. Zoom-Benutzeroberfläche
Mit dieser Einstellung kann die Benutzeroberfläche vergrößert werden, um sie an hochauflösende Bildschirme anzupassen. Damit die Änderung wirksam wird, muss die Software neu gestartet werden.
3.2.4. Hexadezimal-Viewer
Die in diesem Abschnitt enthaltenen Einstellungen definieren die Standardkodierung, in der die symbolische Bytendarstellung im Hexadecimal Viewer angezeigt wird, die maximale Anzahl der über die Systemzwischenablage kopierten Bytes und die maximale Anzahl von Bytes, die im Hexadecimal-Editor für "Rückgängig" verwendet werden.
3.2.5 Explorer
Die in diesem Abschnitt verfügbaren Einstellungen legen die maximale Anzahl von Objekten fest, die auf einer einzelnen "Seite" des Explorers dargestellt werden, und die maximale Anzahl von Suchergebnissen, die von einem einzelnen Suchvorgang zurückgegeben werden. Bei niedrigeren Werten wird Speicherplatz gespart und die Geschwindigkeit erhöht, während bei höheren Werten mehr Objekte bearbeitet werden können. Die empfohlenen Werte finden Sie im Hinweisbereich: Wählen Sie die Kopfzeile des entsprechenden Felds aus, um sie anzuzeigen. Die Änderungen werden auf alle nachfolgenden Vorgänge angewendet. Außerdem ist es möglich, die Standardaktion für das Tool "Ansicht" einzurichten: Zu den Aktionen gehören das Öffnen im internen Viewer oder das Kopieren der Datei in den Ordner für temporäre Dateien und das Starten unter Verwendung der standardmäßig zugeordneten Anwendung.
3.2.6 Wiederherstellung von Dateien (Kopieren)
Dieser Abschnitt enthält alle erforderlichen Einstellungen für das Kopieren wiederhergestellter Dateien: Die Standardaktion, die beim Vorhandensein doppelter Dateien ausgeführt wird, ob solche Konflikte von der Software protokolliert werden, was geschieht, wenn eine Datei oder ein Ordner nicht erstellt werden kann Am angegebenen Zielspeicherort, in welchem Format wiederhergestellte verschlüsselte NTFS-Dateien (EFS-Dateien) gespeichert werden und ob erweiterte Attribute wiederhergestellt werden (für HFS +).
3.2.7 RAID-Standardeinstellungen
Dieser Abschnitt enthält Einstellungen zum Lesen und Assemblieren von RAID-Sets: Ob die Software angeschlossenes RAID erkennt und versucht, bekannte Konfigurationen automatisch zusammenzustellen, aktualisieren unvollständiges RAID, wenn der fehlende Bestandteil erkannt wird, oder versuchen, RAID asynchron zu lesen, wenn dies möglich ist.
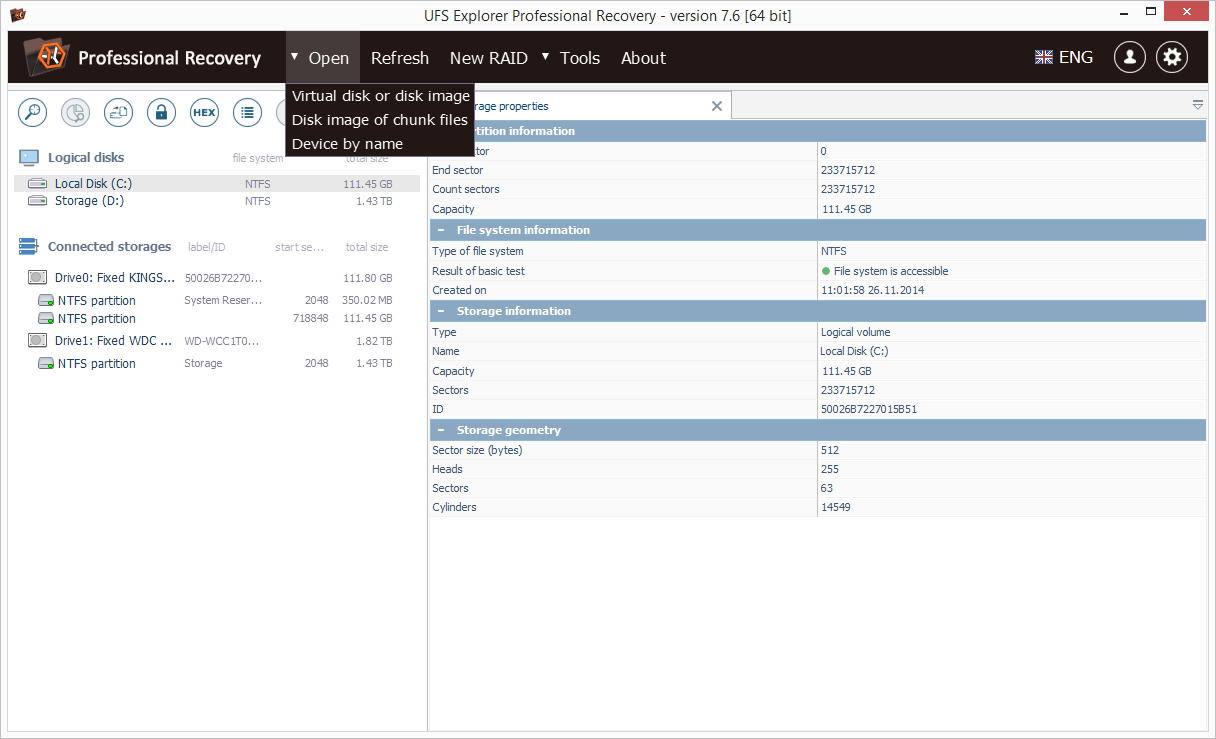
3.3 Operationen
Beim Start wird das Hauptfenster des Programms angezeigt, das das Hauptmenü (oben in der Nähe), die Navigationsstruktur der Speicher (ein Fenster auf der linken Seite der Benutzeroberfläche) und den Arbeitsbereich (Hauptprogrammbereich rechts) enthält.. Standardmäßig wird im Arbeitsbereich die Registerkarte "Speichereigenschaften" angezeigt, die verschiedene Informationen zu den verbundenen Speichern enthält: für physische Festplatten - Typ, Name, Kapazität, Anzahl der Sektoren, ID, Speichergeometrie, für logische Festplatten - Anfang / Ende, Nummer Zusätzlich zu den oben genannten Informationen über den physischen Speicher, zu dem er gehört, werden Informationen über Sektoren, Kapazität und verschiedene Dateisystemeigenschaften sowie zusätzlich anerkannte Technologien bereitgestellt. Diese Registerkarte kann auch mit Hilfe des Werkzeugs "Eigenschaften anzeigen" in der Symbolleiste über der Navigationsstruktur oder über das Kontextmenü des Speicherkontexts geöffnet werden.
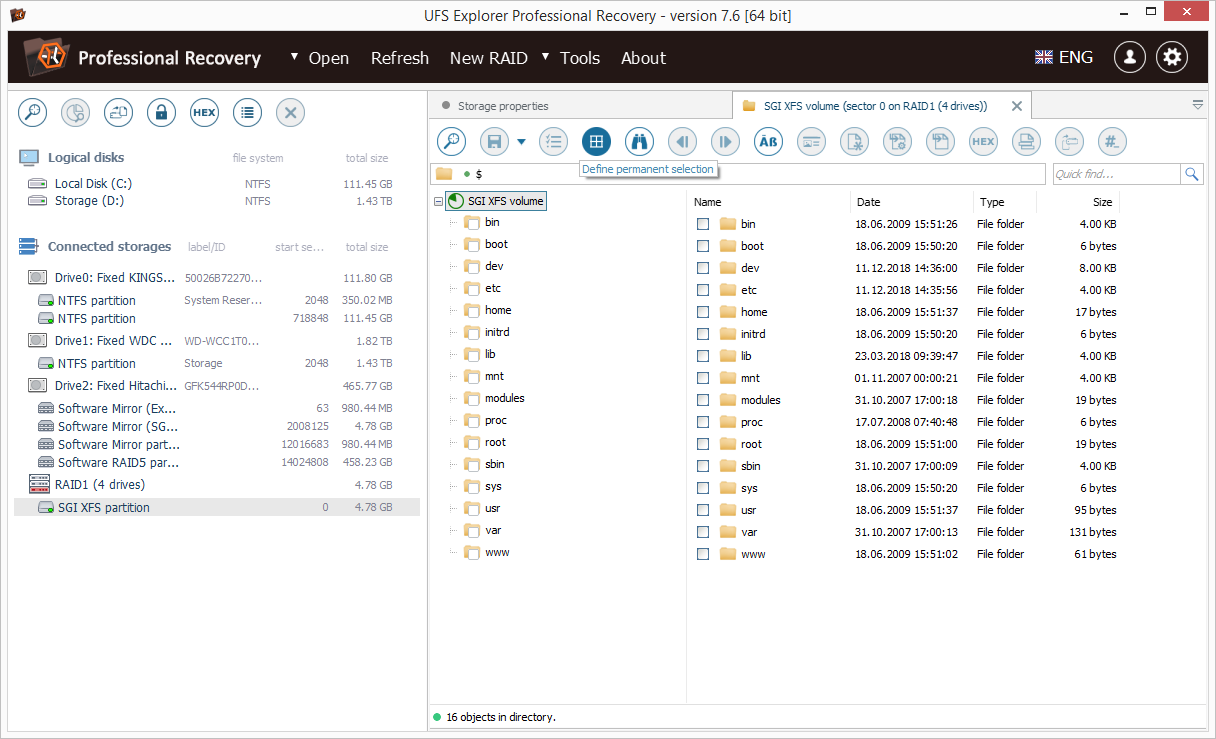
Um Zugriff auf den Inhalt eines Speichers zu erhalten, aktivieren Sie die gewünschte Festplattenpartition im Navigationsbaum der Speicher, oder wählen Sie im Kontextmenü die Option "Dateisystem erkunden". Die Software zeigt die Registerkarte "Explorer" für das ausgewählte Dateisystem im Arbeitsbereich an. Bei der Navigation im Explorer-Stil können Sie zu einem bestimmten Ordner navigieren, die gewünschten Dateien mit dem Werkzeug "Dauerhafte Auswahl definieren" suchen, auswählen und mit dem Werkzeug "Auswahl speichern" in der Symbolleiste "Explorer" oder mit "Speichern" speichern object to ... "Kontextmenüoption für jede der Dateien.
Jede Datei kann auch nach der Aktivierung mit einer Tastatur oder Maus "geöffnet" werden. Dadurch wird die Datei entweder in den Ordner unter "Temporärer Dateipfad" kopiert und mit dem standardmäßig auf Ihrem Computer installierten zugehörigen Programm geöffnet. Alternativ kann die Datei im internen Viewer auf einer neuen Registerkarte geöffnet werden. Dies hängt von den in den Softwareeinstellungen festgelegten Einstellungen ab.
3.3.1 Speichernavigation
Der Baum enthält zwei Hauptcontainer: "Logische Datenträger", die alle verfügbaren logischen Datenträger enthalten, und "Verbundene Speicher", die alle verbundenen physischen Geräte, Datenträgerabbilder, komplexen Speicher und übergreifende Datenträger auflisten.
Speicherbetrieb
Das Element "Öffnen" im Hauptmenü enthält drei Unterelemente, mit denen Sie ein Festplattenabbild oder eine virtuelle Festplatte, ein Festplattenabbild von Chunk-Dateien oder ein Blockgerät manuell öffnen können, indem Sie den vollständigen Pfad angeben.
Mit dem Unterpunkt "Virtuelle Festplatte oder Festplattenabbild" können Sie alle unterstützten Festplattenabbilder oder Dateien der virtuellen Festplatte öffnen. Darüber hinaus können Sie auch eine zuvor gespeicherte RAID-Konfiguration und virtuelle Image-Dateien der Runtime-Software (* .vim-Dateien) öffnen.
Der Unterpunkt "Das Plattenabbild der Chunk-Dateien" ermöglicht das Überspannen mehrerer Plattenabbilddateien und kann in Fällen nützlich sein, in denen ein einzelnes Festplattenabbild beispielsweise in mehrere Teile aufgeteilt ist, da seine Größe sehr groß ist.
Der Unterpunkt "Device by name" ermöglicht das Öffnen eines physischen Speichers durch Angabe seines betriebssystemspezifischen Gerätenamens. In Microsoft Windows können Sie ein Volume öffnen, indem Sie seinen Einhängepunkt angeben (z. B. "E:"). Um auf physische Laufwerke zugreifen zu können, müssen Sie die Software als lokaler Administrator ausführen.
Die im UFS Explorer geöffneten Speicher können mit Hilfe des Werkzeugs "Speicher schließen" aus der Symbolleiste über dem Navigationsbaum der Speicher geschlossen werden oder die Option "Speicher schließen" aus dem Kontextmenü des Speichers.
Das Element "Aktualisieren" im Hauptmenü setzt die Struktur der angefügten Speicher zurück. Die Liste der angefügten Speicher wird aktualisiert und enthält alle erkannten Speicher, auch die zuvor geschlossenen (außer geschlossene Festplatten-Images und manuell zusammengebaute RAID). Diese Operation gilt nicht für die Registerkarten, die bereits in UFS Explorer geöffnet wurden: Ein Speicher wird geschlossen, nachdem die letzte Registerkarte dieses Speichers geschlossen wurde.
Falls das Betriebssystem Software-RAID verwendet, wird es als Satz seiner Komponenten angezeigt. Um ein solches RAID zu öffnen, verwenden Sie den Unterpunkt "Device by name" des Menüelements "Open" und öffnen Sie das RAID, indem Sie den Gerätenamen oder den Einhängepunkt angeben (z. B. "E:" unter Windows oder "/ dev / lvm / vg0"). unter Linux).
Festplattenpartitionen
Eine einzelne physische Festplatte kann in mehrere Partitionen unterteilt sein. Der Zweck dieser Unterteilung ist die Datenisolation (von anderen Daten oder Betriebssystemen), die Installation verschiedener Betriebssysteme auf demselben physischen Laufwerk usw.
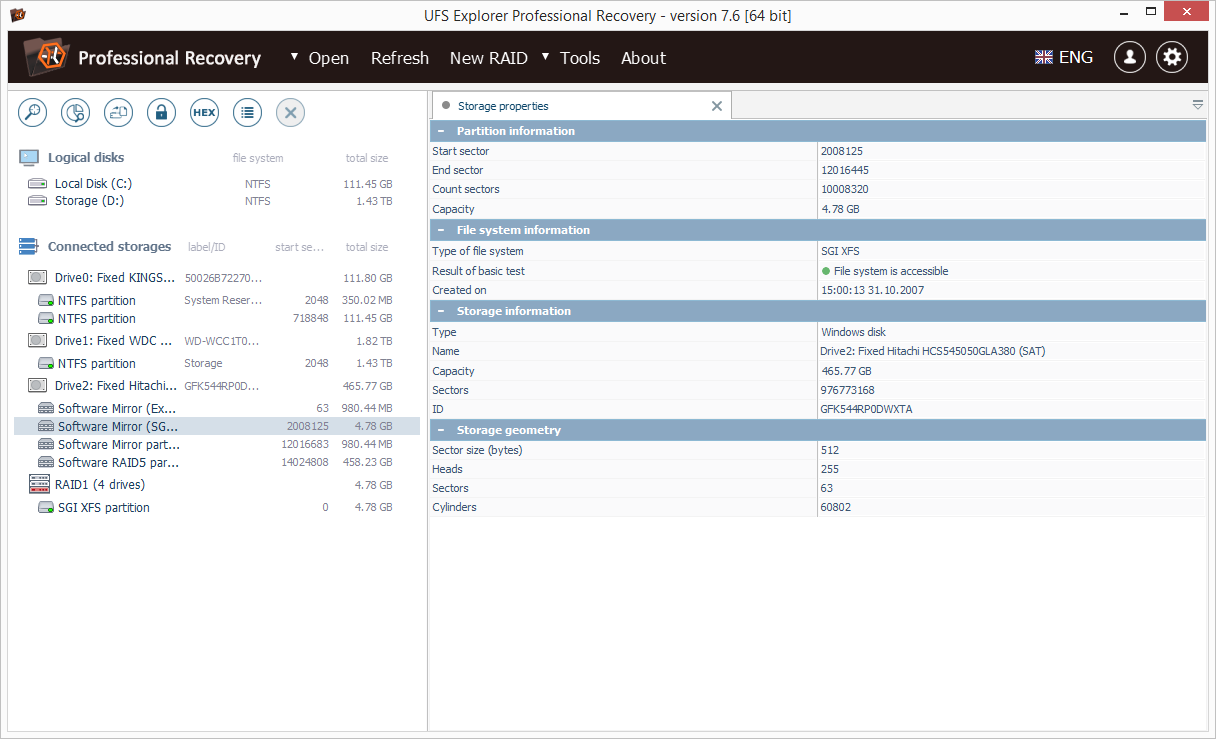
Die Software zeigt Festplattenpartitionen unter dem entsprechenden "Laufwerk" -Element (einschließlich derjenigen mit unbekannten oder nicht unterstützten Dateisystemen). Der Name einer Partition spiegelt den Typ eines darauf angewendeten Dateisystems oder die implementierte Speichertechnologie wider. Der Startsektor und die Gesamtgröße werden neben jeder Festplattenpartition angegeben. Weitere Details zu einer Partition finden Sie auf der Registerkarte Speichereigenschaften.
Das Dateisystem-Symbol zeigt den Zustand an: Ein grünes Symbol bedeutet, dass auf das Dateisystem zugegriffen werden kann, das gelbe kann Probleme anzeigen, das rote zeigt an, dass Probleme vorliegen, und das graue Symbol bedeutet, dass das Dateisystem nicht erkannt werden kann. Das Vorhängeschloss-Symbol bedeutet, dass das Volume verschlüsselt wird, während für die verwendeten zusätzlichen Speichertechnologien auch spezielle Symbole angezeigt werden.
Die Software zeigt keine Informationen zum Einhängepunkt des Dateisystems an. Beispielsweise kann Laufwerk "C:" einfach als NTFS-Partition einer bestimmten Größe angezeigt werden.
Ein Volume kann anhand des Datenträgers identifiziert werden, zu dem es gehört, Größe, Typ oder Dateisystem sowie anhand des Inhalts der Dateien / Ordner.
Nachdem eine Partition aktiviert wurde, öffnet die Software ihr Dateisystem in einer neuen Registerkarte "Explorer".
Disk Image erstellen
Wenn eine Festplatte defekt zu sein scheint, wird dringend empfohlen, ein Image zu erstellen und eine weitere Datenwiederherstellung mit dieser Disk-Image-Datei durchzuführen.
Der UFS-Explorer ermöglicht das Erstellen einer Bit-zu-Bit-Disk-Image-Datei eines Speichers mit einem speziellen Werkzeug aus der Symbolleiste oberhalb der Speichernavigationsstruktur oder der Kontextmenüoption. Wählen Sie dazu die benötigte Diskette aus und wählen Sie das Werkzeug "Disk-Image-Datei speichern" oder klicken Sie mit der linken Maustaste auf den Speicher und wählen Sie die entsprechende Kontextmenüoption. Das Tool ermöglicht das Speichern eines partiellen Plattenabbilds, indem ein Datenbereich in Sektoren definiert wird.
Ein partielles Festplatten-Image kann auch mit Hilfe des Hexadezimal-Viewers erstellt werden. Wählen Sie dazu die Kontextmenüoption "Hexadezimal-Inhalt anzeigen" (oder das Werkzeug aus der Symbolleiste mit demselben Namen), wählen Sie einen bestimmten Speicherbereich aus, klicken Sie auf die Schaltfläche "Inhalt speichern unter". Wenn Sie dazu aufgefordert werden, wählen Sie zum Speichern nur die aktuelle Auswahl ".
Ein vollständiges Festplatten-Image kann in der Software mit dem Unterpunkt "Virtuelle Festplatte oder Festplatten-Image" aus dem Menüpunkt "Öffnen" geöffnet werden, während teilweise Platten-Images mit Hilfe der Menüoption "Festplatten-Image von Chunk-Dateien" zusammengestellt werden können.
Fehlende Partitionen definieren
Die Software ermöglicht die Definition einer fehlenden Partition sowohl manuell als auch durch automatisiertes Scannen. Um die Registerkarte "Partitionen" für eine beliebige physische Festplatte zu öffnen, doppelklicken Sie einfach auf diese Festplatte oder wählen Sie sie aus und wählen Sie das Werkzeug "Partitionen verwalten" in der Symbolleiste über der Navigationsstruktur der Speicher. Die Werkzeuge zum Arbeiten mit Partitionen stehen in der Symbolleiste des Abschnitts "Partitionen" zur Verfügung.
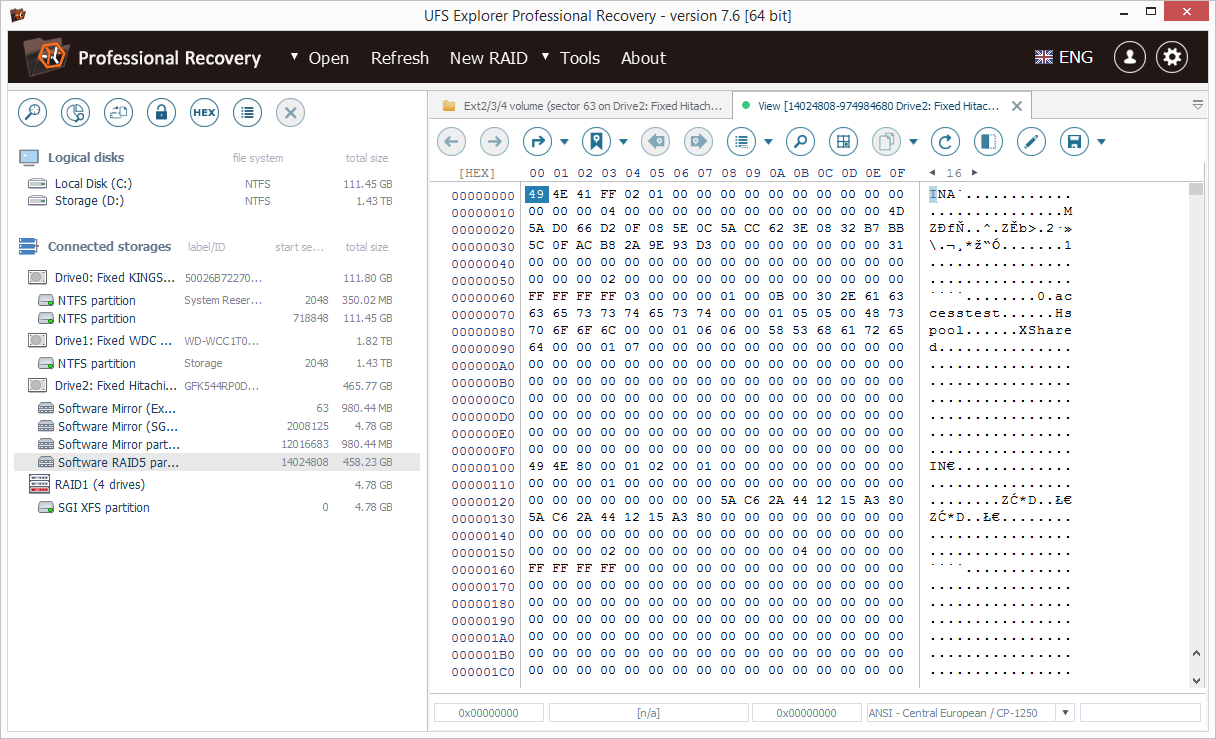
Der Abschnitt "Partitionen" wird mit dem Element Hexadecimal Viewer synchronisiert: Wenn eine neue, standardmäßig definierte Partition analysiert wird, wird die aktuelle Position im Hexadecimal Viewer verwendet. Wenn eine Festplattenpartition ausgewählt ist, navigiert der Hexadezimal-Viewer zum Startort der Partition auf der Festplatte.
Um eine Partition manuell zu definieren, verwenden Sie das Werkzeug "Bereich durch Angabe des Bereichs manuell definieren" in der Symbolleiste der Registerkarte "Partitionen". Zuvor finden Sie die Partition möglicherweise im Hexadezimal-Viewer. In diesem Fall kann die Software Partitionsparameter (wie Start, Größe, Dateisystemtyp) automatisch erkennen, wenn diese Informationen von der Software erkannt werden.
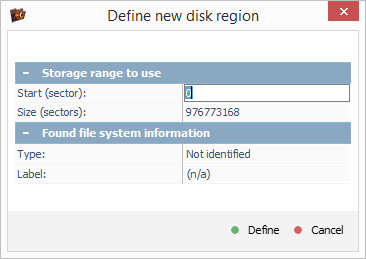
Die automatisierte Suche nach verlorenen Partitionen ist über das Tool "Nicht erkannte Partitionen nach Metadaten suchen" verfügbar. Wenn Sie einen neuen Scan gestartet haben, sollten Sie einen zu analysierenden Plattenbereich und die Dateisystemtypen angeben, nach denen gesucht werden soll. Wenn das Dateisystem erkannt wird, fügt die Software die Festplattenpartition automatisch der Liste der Festplattenpartitionen und dem Partitionselement unter dem Laufwerk im linken Navigationsbereich der Speicher hinzu.
Die Liste der Partitionen kann später mit den Tools "Liste in Datei speichern" / "Liste aus Datei laden" gespeichert und wiederhergestellt werden. Es wird empfohlen, die Partitionsliste nach einem erfolgreichen Scan zu speichern, um ein wiederholtes Scannen nach dem Neustart der Software zu vermeiden.
3.3.2 Explorer verwenden
Die Registerkarte "Explorer" für das Dateisystem kann mit einem Doppelklick auf eine Festplattenpartition oder mit Hilfe des Kontextmenüs "Dateisystem durchsuchen" geöffnet werden.
Wenn die Software das Dateisystem nicht erkennt, wird der Hexadezimal-Viewer für diesen Speicher geöffnet.
Dateien und Ordner im Explorer werden als sortierte Listen dargestellt, die den Datei- / Ordnernamen, den Typ, die Größe und das Änderungsdatum enthalten. Sie können die Liste neu sortieren, indem Sie auf die Spaltenüberschrift klicken.
Zur Vereinfachung der Navigation enthält der Explorer eine schnelle Navigationsleiste mit Unterstützung der Navigation nach Navigationsverlauf, Navigation zu übergeordneten Ordnern oder durch Eingabe eines vollständigen Pfads.
Auf der linken Seite der Registerkarte "Explorer" befindet sich eine Ordnerstruktur.
Wenn ein Ordner aktiviert ist, navigiert die Software zu diesem Ordner. Wenn eine Datei aktiviert ist, öffnet das Programm sie abhängig von den in den Softwareeinstellungen festgelegten Einstellungen entweder im internen Viewer oder kopiert sie in den Ordner für temporäre Dateien und öffnet sie mit der zugehörigen installierten Anwendung.
Sie können Dateien und Ordner in einem bestimmten "lokalen" Ordner speichern, indem Sie sie auswählen und die Kontextmenüoption "Objekt speichern unter ..." wählen.
Sie können im Explorer mehrere Objekte zum Kopieren auswählen, indem Sie beim Auswählen eines Objekts in der Liste die Tasten "Umschalt" oder "Strg" gedrückt halten.
Wenn Sie eine komplexere Regel zum Kopieren von Dateien benötigen, verwenden Sie eine "Massenkopie" -Operation.
Explorer-Seiten
Wenn die Anzahl der Dateien und Ordner die in den Softwareeinstellungen angegebene Höchstzahl überschreitet, verwendet der Explorer "Pages", um alle Dateien anzuzeigen. In der Symbolleiste werden die Schaltflächen für die Navigation "Vorherige" und "Nächste" und die Schaltfläche zum Navigieren zu einer Seite um eine bestimmte Nummer aktiviert.
Um alle Daten aus einem solchen Ordner zu kopieren, können Sie entweder eine "Massenkopie" -Operation verwenden oder eine Kopie für den übergeordneten Ordner anwenden.
Massenkopieren
Die Option wird über die Schaltfläche "Feste Auswahl definieren" der Explorer-Symbolleiste aktiviert. Dadurch wird sowohl die Liste der Dateien als auch die Ordnerstruktur in den "Kontrollkästchenmodus" geändert, sodass Sie Dateien und Ordner zum Kopieren auswählen können.
Die Kopierregel ist definiert als:
- Eine Datei oder ein Ordner, der mit einem Kontrollkästchen ausgewählt wurde, wird kopiert.
- Wenn ein Kontrollkästchen aus der Datei entfernt wurde, wird es nicht kopiert.
- Wenn ein Ordner ausgewählt ist, wird er zusammen mit seinem Inhalt mit Ausnahme der nicht ausgewählten Dateien und Ordner kopiert.
Wenn Sie alle erforderlichen Dateien / Ordner ausgewählt haben, drücken Sie "Auswahl speichern", um den Kopiervorgang zu starten. Die Auswahl kann mit Hilfe der Schaltfläche "Dauerauswahl löschen" abgebrochen werden.
Suchen Sie nach Dateien und Ordnern
Die Funktion ist als "Schnellsuche" -Feld verfügbar: Geben Sie einfach eine Unterzeichenfolge des Dateinamens im Suchfeld an. Sie können auch die erweiterte Suche verwenden: das Werkzeug "Dateien und Ordner suchen" in der Symbolleiste des Registers "Explorer", das Kontextmenü des Ordners "Dateien und Ordner suchen" oder die Tastenkombination "Strg + F".
Die Schnellsuche verwendet eine Zeichenfolge als Teil des Dateinamens und verwendet die Einstellungen für die Groß- und Kleinschreibung des aktuellen Dateisystems.
Für die erweiterte Suche können Sie eine vollständige Maske für den Dateinamen angeben (einschließlich der "Wildcard" -Symbole * und?). Sie können auch eine Regel für die Dateigröße und für die Aufnahme von Dateien und Ordnern in das Suchergebnis definieren.
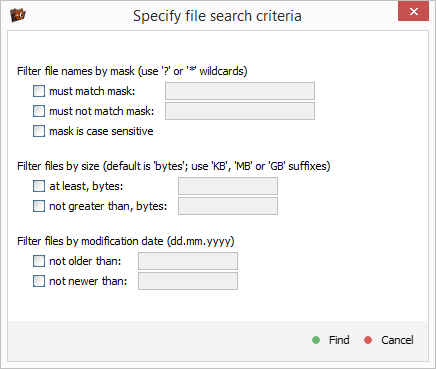
Der Suchvorgang wird auf einer neuen Registerkarte "Suchergebnis" gestartet und läuft über alle Unterordner des ausgewählten Ordners, bis alle Unterordner verarbeitet werden oder die maximale Anzahl der gefundenen Objekte erreicht ist.
Die neue Suche wird auf derselben Registerkarte gestartet, wenn der vorherige Suchvorgang abgeschlossen ist und die Option "Auf neuer Registerkarte öffnen" nicht angegeben ist.
Sie können von der Registerkarte "Suchergebnisse" zur Registerkarte "Explorer" navigieren, indem Sie den Ordner öffnen, der das ausgewählte Objekt enthält. Die Software kopiert keine Dateien / Ordner von der Registerkarte mit den Suchergebnissen.
Datengröße
Bevor Sie mit dem Kopieren von Dateien und Ordnern beginnen, wird empfohlen, zu prüfen, ob die Größe der ausgewählten Daten mit dem auf dem Zielspeicher verfügbaren freien Speicherplatz übereinstimmt. Sie können das Werkzeug "Größe und Test auswerten" in der Symbolleiste der Registerkarte "Explorer" oder dieselbe Option verwenden, die im Kontextmenü der Ordner- oder Objektgruppe angezeigt wird.
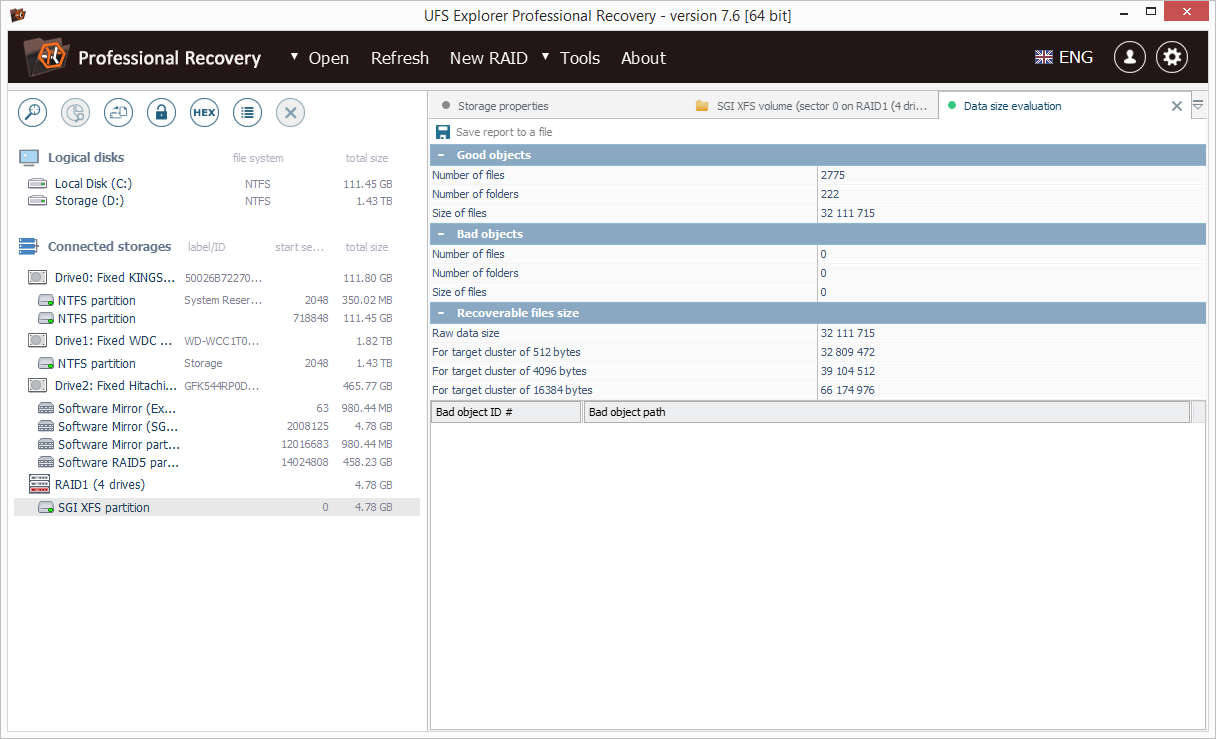
Das Tool ermöglicht sowohl das Auswerten der Datengröße als auch das Testen der Dateisystemkonsistenz. Wenn ein Dateisystem-Konsistenzfehler erkannt wird, wird empfohlen, die Wiederherstellung des Dateisystems fortzusetzen.
Ordner-Baumleiste
Das Bedienfeld enthält Informationen zur aktuell geöffneten Partition, zum Dateisystem und zum Ordner für eine schnelle Navigation. Wenn im linken Bereich ein Ordner ausgewählt wird, wird dieser im Explorer geöffnet. Diese Funktion kann zur schnellen Navigation durch verschiedene Ordner verwendet werden.
Das Ordner-Kontextmenü enthält alle im Explorer für den Ordnerdatensatz verfügbaren Tools. Wenn sich der Explorer im Modus "Massenkopie" befindet, können Sie Ordner durch Doppelklicken auf den Baum auswählen bzw. die Auswahl aufheben.
3.3.3 Wiederherstellung verlorener Dateien
Die Suche nach verlorenen Dateisystemen wurde im Abschnitt Fehlende Partitionen definieren beschrieben. In diesem Abschnitt wird die Wiederherstellung verlorener und gelöschter Dateien beschrieben (einschließlich Wiederherstellung gelöschter Dateien durch Benutzer, Wiederherstellung nach Format, Beschädigung des Dateisystems usw.).
Die Wiederherstellung verlorener Dateien steht als Werkzeug "Nach verlorenen Daten suchen" in der Symbolleiste über dem Speicher-Navigationsbaum und der Symbolleiste "Explorer" sowie als Option im Kontextmenü der Partition zur Verfügung.
Wiederherstellungsprozess
Das Tool "Nach verlorenen Daten suchen" aktiviert die Registerkarte "Wiederherstellung", in der die Parameter für die Dateisystemprüfung angegeben oder geändert werden.
Die Registerkarte besteht aus einem Einstellungsbereich, der verschiedene Einstellungen enthält, z. B. Scanbereich, zu suchende Dateisystemtypen, Kodierungsoptionen für Dateinamen, IntelliRAW-Verwaltung und die Schaltflächen zum Starten des Wiederherstellungsvorgangs oder zum Fortsetzen eines gespeicherten Scans.
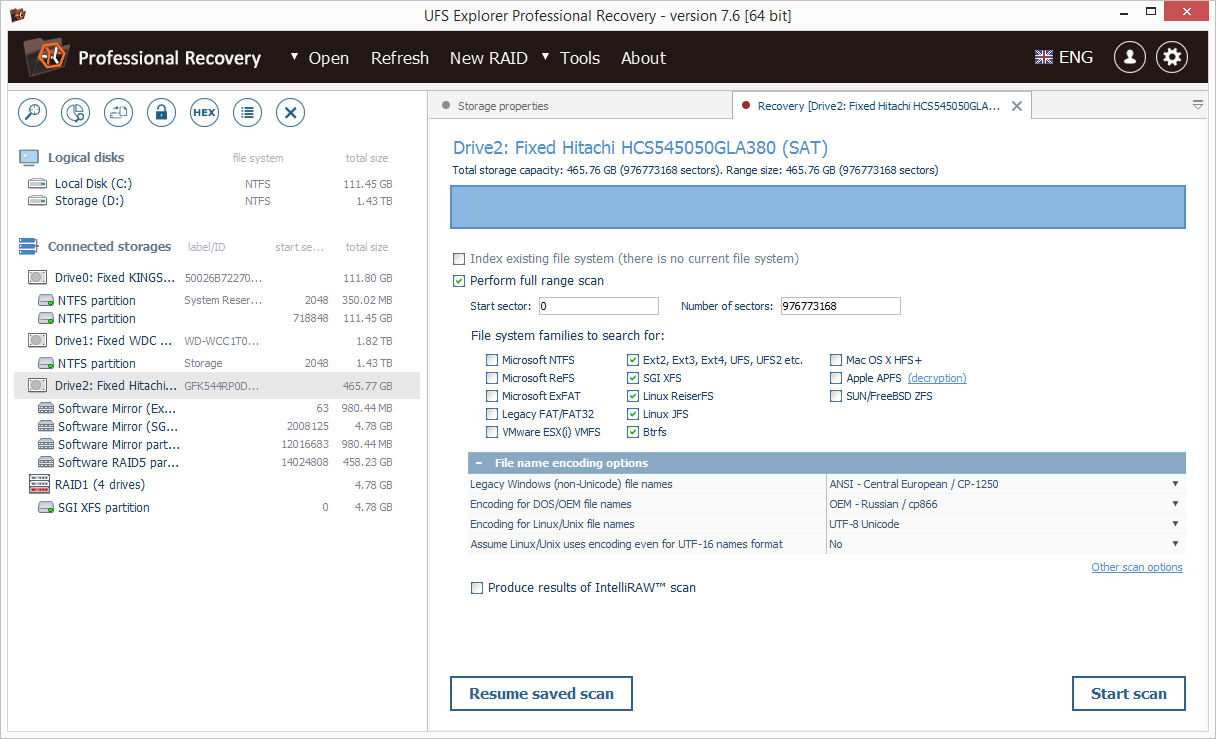
Suchen Sie nach Dateisystemvariationen, wenn die Dateisystemkonfiguration oder der Dateityp geändert wurde und Sie den vorherigen Dateisystemstatus wiederherstellen möchten. Das Tool ermöglicht die Definition von Dateisystemtypen, nach denen gesucht werden soll, und nach Varianten.
Beispiel 1: Ein externes FAT32-formatiertes Laufwerk mit einigen Benutzerdaten wurde mit NTFS neu formatiert. Ziel ist die Wiederherstellung von Daten, die auf FAT32 gespeichert wurden. Standardmäßig zeigt die Software nur einen Datensatz für das NTFS-Dateisystem an. Wählen Sie "FAT" als Dateisystem, um nach dem Scan zu suchen und ihn auszuführen. Die Software sollte die Variation "FAT" erkennen und der Scanvorgang kann abgebrochen werden, um die Datenwiederherstellung vom Dateisystem "FAT" aus durchzuführen.
Beispiel 2: NAS Buffalo Terastation (4 × 1 TB) wurde als RAID0 für Geschwindigkeit konfiguriert (die ungefähre Größe der Datenpartition beträgt 3,8 TB), wurde jedoch nach einem Ausfall auf die Werkseinstellung von RAID 5 wiederhergestellt (die ungefähre Größe der Datenpartition ist 2,7 TB). Die Adresse der Cluster wurde geändert (die Clusteradresse in XFS hängt von der Größe des Dateisystems ab). Um Dateien aus dem alten Zustand wiederherzustellen, sollten Sie RAID als RAID0 zusammenstellen, das Dateisystem ist jedoch immer noch 2,7 TB groß (das neue Dateisystem hat das vorhandene überschrieben). Um Dateien und Ordner zu finden, muss die Software zunächst die 3,8-TB-Dateisystemvariante finden. Wählen Sie dazu "SGI XFS" als Dateisystem zum Scannen, führen Sie den Scan aus und warten Sie, bis die 3,8-TB-XFS-Variante erkannt wird. Danach können Sie den Scan abbrechen und die gerade gefundene Dateisystemvariante wiederherstellen.
Wenn Sie alle Einstellungen festgelegt haben, klicken Sie einfach auf die Schaltfläche "Scan starten" in der rechten unteren Ecke der Registerkarte "Wiederherstellung".
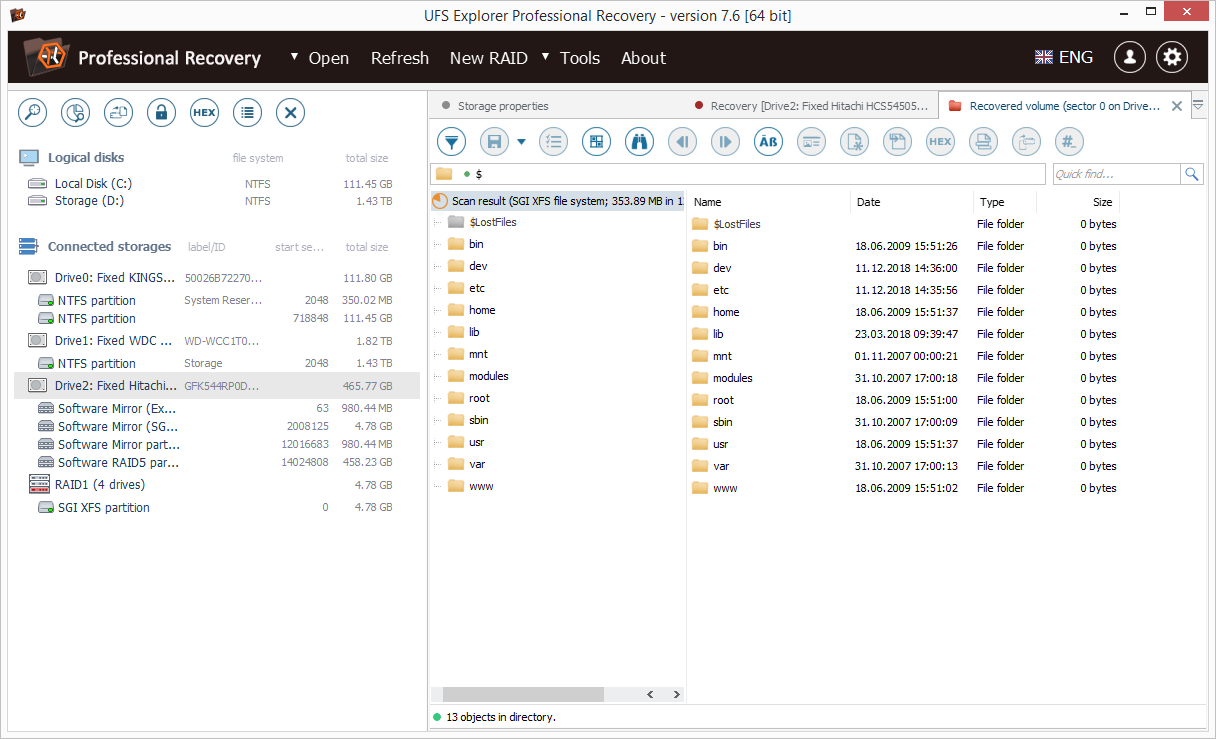
Der Scan kann einige Zeit dauern. Nach Abschluss zeigt die Software die Liste der wiederhergestellten Volumes an. Um ein Volume im Explorer zu öffnen, doppelklicken Sie darauf oder wählen Sie es in der Liste aus und drücken Sie "Ausgewähltes Element öffnen". Um es als virtuelle Dateisystemdatei zu speichern, die später mit Hilfe des Untermenüs "Virtuelle Festplatte oder Datenträgerabbild" des Eintrags "Öffnen" des Hauptmenüs geöffnet werden kann, wählen Sie es aus und klicken Sie auf die Schaltfläche "Diesen Eintrag speichern". Verwenden Sie die Schaltfläche "Dieses Objekt zerstören", um ungültige oder nicht benötigte Scanergebnisse zu löschen.
Eine neue Registerkarte "Explorer" für das Scanergebnis weist geringfügige Unterschiede zur Hauptoberfläche des Explorers auf.
Speichern eines Scanergebnisprojekts
Um den Verlust von Scanergebnissen durch Software- oder Hardwarefehler zu vermeiden, wird dringend empfohlen, das Scanergebnisprojekt zu speichern, damit Sie den Speicher nicht noch einmal scannen müssen, was bei großen und langsamen Speichern zu Abweichungen führen kann. Wenn Sie die Wiederherstellung nach dem Neustart der Software fortsetzen müssen, können Sie das Scanergebnis einfach laden. Diese Option ist im Kontextmenü der Partition als "Gespeichertes virtuelles Dateisystem laden" verfügbar. Ein solches Scan-Ergebnis kann auch mit Hilfe des Untermenüs "Virtuelle Festplatte oder Image" unter "Öffnen" des Hauptmenüs geöffnet werden. Wenn die letztere Methode verwendet wird, sucht die Software nach einem passenden Speicher und lädt das Scanergebnis als virtuelle Partition des Speichers. Wenn der Speicher nicht gefunden wurde,
UFS Explorer Professional Recovery ermöglicht auch das Unterbrechen des Speicherscans, das Speichern als Datenbank für den Scanstatus und die spätere Fortsetzung. Um den Scan zu unterbrechen, klicken Sie auf die Schaltfläche "Scan anhalten" in der unteren linken Ecke des Arbeitsbereichs und speichern Sie ihn mit der Schaltfläche "Aktuellen Status speichern". Um den Scan fortzusetzen, drücken Sie unten links auf der Registerkarte "Wiederherstellung" auf "Gesicherten Scan fortsetzen".
Wiederherstellen der Dateien
Dateien, die ein Scanergebnis darstellen, können wie ein Originaldateisystem durchsucht und kopiert werden. Dies bedeutet, dass erforderliche Dateien und Ordner mit den gleichen Tools gespeichert werden können, die im Explorer verfügbar sind
Wichtig: Speichern Sie niemals wiederhergestellte Dateien im Quellspeicher. Die Dateidaten (Inhalt) für die Wiederherstellung werden immer noch vom Quelllaufwerk gelesen. Dies bedeutet, dass die Software sie möglicherweise überschreiben kann. Verwenden Sie dazu einen zusätzlichen Speicher.
3.3.4 Disk-on-Disk
Die Funktion ermöglicht den Zugriff auf Dateien und Ordner auf einer virtuellen Festplatte oder einem Festplatten-Image, das sich an einem unzugänglichen Speicherort befindet, ohne vorher kopiert zu werden, als wäre es eine "lokale" temporäre Festplatten-Image-Datei. Die unterstützten Situationen umfassen:
- virtuelle Laufwerke, die durch Ausführen von Virtualisierungssoftware in einem Dateisystem gesperrt sind;
- virtuelle Festplatten auf ESX (i) VMFS-Partitionen;
- Festplatten-Images oder virtuelle Festplatten, die auf Partitionen gespeichert sind und vom Host-Betriebssystem nicht unterstützt werden;
- Plattenimages, die in Dateisystemen von Plattenimages gespeichert sind.
Die Verschachtelungsebene für die "Disk-on-Disk" -Funktion ist nicht begrenzt.
Um die Funktion zu verwenden, müssen Sie:
1. Öffnen Sie den Speicher (z. B. eine Festplattenpartition) im UFS Explorer.
2. Suchen Sie eine virtuelle Festplatte oder eine Image-Datei.
3. Wählen Sie die Datei aus und wählen Sie das Werkzeug "Dateien als Disk Image öffnen".
Die Software öffnet den Speicher wie jede andere Image-Datei. Wenn das Festplatten-Image ein unterstütztes Dateisystem enthält, wird es erkannt. Wenn es sich bei den in diesem Image gespeicherten Dateien auch um Festplatten-Images handelt, können diese auch mit Hilfe des Tools "Datei als Disk-Image öffnen" geöffnet werden. Eine Disk-on-Disk kann auch als Teil von RAID verwendet werden. Eine solche RAID-Konfiguration kann jedoch nicht gespeichert werden.
3.3.5 Dateidatenanalyse
Die UFS Explorer Professional Recovery-Software ermöglicht nicht nur das Auffinden verlorener Daten, sondern auch die Bewertung der Dateisystemkonsistenz und die Diagnose logischer Ursachen, die zu Datenschäden führen. Die speziellen Werkzeuge für die Analyse von Dateizuordnungen sind:
- das Tool "Gehe zu Beschreibung auf der Festplatte" in der Symbolleiste "Explorer" und die Kontextmenüoption "Objekt", mit der der Objektdeskriptor gefunden und im Hexadezimal-Viewer angezeigt werden kann
- das Tool "Gehe zum Start der Datei auf der Festplatte" in der Symbolleiste des Registers "Explorer". Die Option und das Kontextmenü des Objekts zeigen auf den Start der Datei / des Ordners auf der Partition.
- Das Werkzeug "In hexadezimalem Viewer öffnen" in der Symbolleiste "Explorer" und im Kontextmenü des Objekts ermöglicht das Öffnen des Inhalts einer Datei oder eines Ordners im Hexadezimal-Viewer zur Analyse.
- Das Werkzeug "On-Disk-Fragmente anzeigen" in der Symbolleiste des Registers "Explorer". Die Option und das Kontextmenü des Objekts ermöglichen das Auffinden und Navigieren in Fragmenten einer Datei oder eines Ordners.
Die verfügbaren Funktionen hängen vom Dateisystemtyp ab. Die Funktionen ermöglichen die Diagnose und Lösung von Dateisystem- oder Speicherlogikproblemen durch Analyse der Datenzuordnung von Dateien und Ordnern.
3.3.6 RAID
UFS Explorer Professional Recovery implementiert alle mit RAID-Wiederherstellung zusammenhängenden Funktionen vollständig. Sie erfordern keine vorherige Aktivierung und sind auch in der Testversion verfügbar.
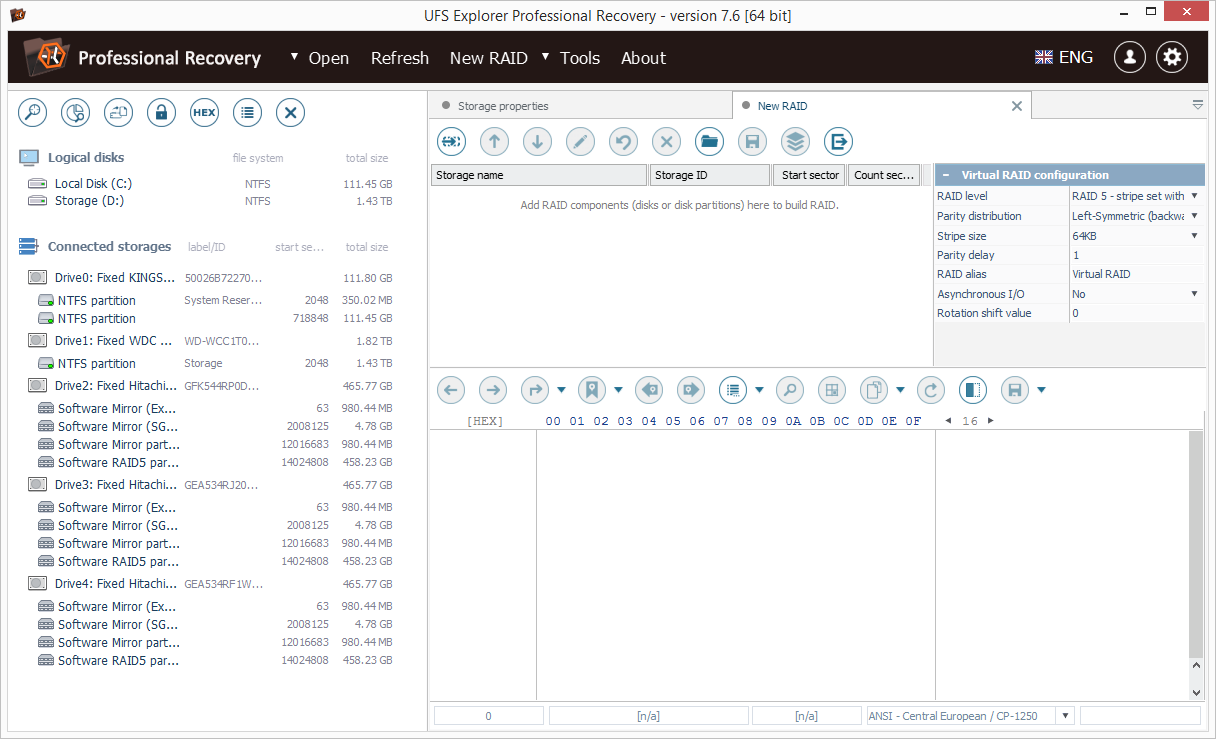
Ein spezielles RAID Builder-Tool ist im Hauptmenü von UFS Explorer Professional Recovery als "Neues RAID" verfügbar. Es öffnet sich eine neue Registerkarte "Neues RAID", die aus einer Symbolleiste, einer Liste von RAID-Komponenten und einem Blatt mit RAID-Eigenschaften besteht. Im unteren Bereich der Registerkarte wird der Bereich "Schnelle Analyse" angezeigt, der als kontextabhängiger Hexadezimal-Viewer implementiert ist.
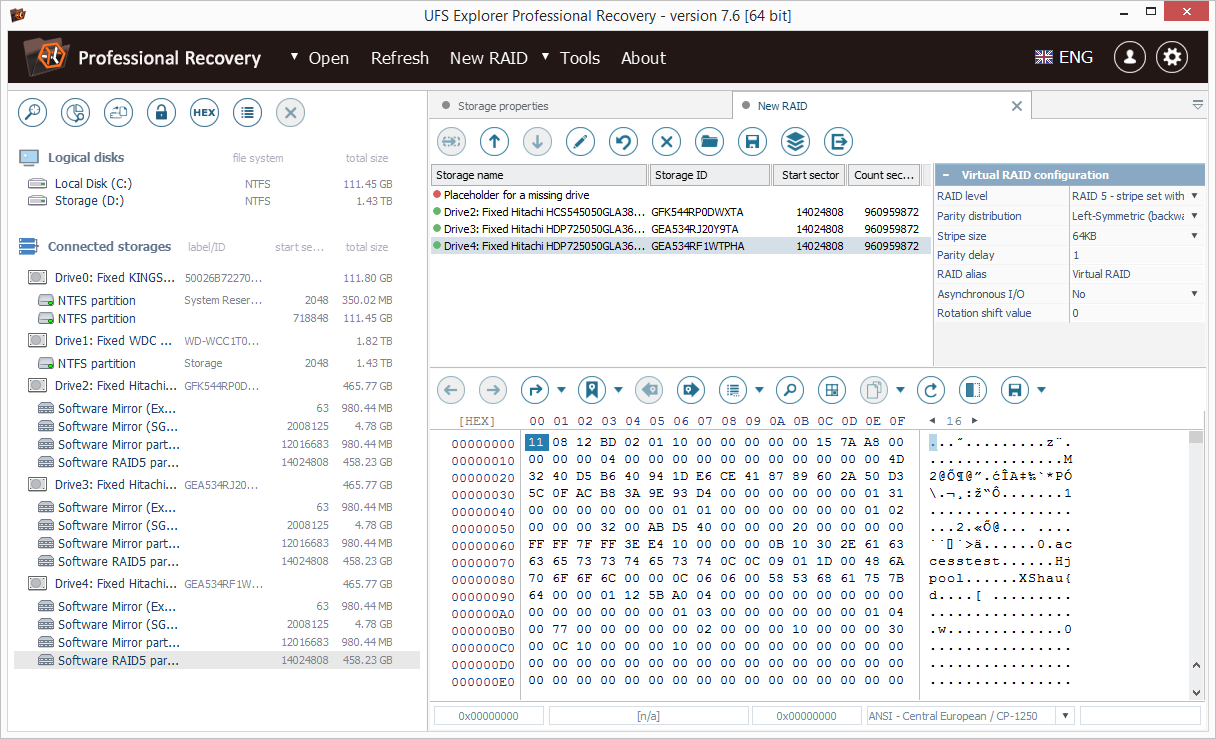
RAID erstellen
Mit dem UFS-Explorer können Sie beliebige RAID-Konfigurationen für den nachfolgenden Datenzugriff oder die Wiederherstellung im virtuellen Modus zusammenstellen. Um ein RAID aufzubauen, sollten Sie alle Komponenten zur Komponentenliste hinzufügen, RAID-Parameter einrichten und auf die Schaltfläche "Dieses RAID erstellen" in der Symbolleiste klicken. Das zusammengestellte virtuelle RAID wird unter den verbundenen Speichern in UFS Explorer angezeigt. Rekonstruktion ohne ein einzelnes Laufwerk wird für RAID 5 und sogar ohne zwei Laufwerke unterstützt - für RAID 6. Dennoch sollte anstelle des fehlenden Bestandteils ein Platzhalter für virtuelle Festplatten hinzugefügt werden, damit das RAID ordnungsgemäß erstellt werden kann. Verwenden Sie dazu die Schaltfläche "Platzhalter hinzufügen, um fehlende Festplatte anzuzeigen" in der Symbolleiste der Registerkarte "Neues RAID".
Hinweis: Eine in UFS Explorer zusammengestellte falsche virtuelle RAID-Konfiguration hat keine Auswirkungen auf die "echte" RAID-Konfiguration. Die Wiederherstellung von Daten aus einem solchen RAID ist jedoch nicht möglich. Um die Datenwiederherstellung erfolgreich abzuschließen, müssen Sie das RAID ordnungsgemäß erstellen. Sie können eine beliebige Anzahl von RAID-Rekonstruktionsversuchen durchführen, da UFS Explorer keine Daten auf den Quellfestplatten ändert.
Hinzufügen einer RAID-Komponente
Alle im linken Bereich des Hauptfensters verfügbaren geöffneten Festplatten oder Image-Images können als RAID-Komponenten verwendet werden. Wenn eine neue Registerkarte "Neues RAID" geöffnet und aktiviert wird, ändert sich das Standardverhalten der Navigationsstruktur der Speicher. Wenn Sie ein Element aktivieren, wird es dem RAID als Komponente hinzugefügt, anstatt den Speicher im Explorer zu öffnen. Dadurch wird auch das Kontextmenü der Festplatte oder der Festplattenpartition um eine neue Option "Zu RAID hinzufügen" erweitert.
Um eine Festplatte oder eine Festplattenpartition als Komponente zu RAID hinzuzufügen, "aktivieren" Sie sie einfach oder verwenden Sie die Kontextmenüoption "Zu RAID hinzufügen". Wenn Sie eine falsche Komponente hinzugefügt haben, wählen Sie sie in der Liste aus und klicken Sie auf die Schaltfläche "Ausgewählte Komponente entfernen" in der Symbolleiste der Registerkarte "Neues RAID".
Um einen Platzhalter für ein fehlendes Laufwerk hinzuzufügen (nur für RAID 5 oder RAID 6), klicken Sie auf die Schaltfläche "Platzhalter hinzufügen", um ein fehlendes Laufwerk anzuzeigen.
Um die Reihenfolge der Speicherkomponenten zu ändern, können Sie schließlich ein Element auswählen und mit den Schaltflächen "Komponente nach oben verschieben" / "Komponente nach unten verschieben" die korrekte Ordinalposition für die ausgewählte Komponente festlegen.
Wenn eine Speicherkomponente eine falsche Größe hat oder Sie die Startposition anpassen sollten, verwenden Sie das Werkzeug "Komponentenbereich bearbeiten".
RAID-Parameter
Sie können jedes Quellmaterial verwenden, um die korrekten RAID-Komponenten zu ermitteln (BIOS-Informationen des RAID-Boards, Konfigurationsdateien, Strukturen auf der Festplatte usw.). Auf jeden Fall sollten Sie die richtigen RAID-Parameter angeben, um intakte Daten wiederherzustellen.
Verschiedene RAID-Level verwenden verschiedene Einstellungen. Das Eigenschaftenblatt des RAID Builder passt sich an die ausgewählte RAID-Stufe an und ermöglicht die Angabe nur der erforderlichen RAID-Parameter.
Für RAID 6 gibt es zusätzliche Parameter (bezogen auf den Redundanzalgorithmus und die Verteilung), die nur angegeben werden sollten, wenn RAID mit fehlenden (ausgefallenen) Laufwerken wiederhergestellt wird.
Kontextbezogene Datenanalyse
Die Daten der ausgewählten Komponente auf der Festplatte werden am unteren Rand des Fensters "Hexadezimal-Viewer" angezeigt. Dies ermöglicht eine schnelle Analyse des Festplatteninhalts und eine visuelle Bestätigung der Reihenfolge der Festplatten. Durch das Wechseln einer Komponente zeigt die Software den Inhalt einer anderen Komponente an derselben Position an. Der Hexadezimal-Viewer ist auch so konfiguriert, dass Tabellensprünge in der Größe eines für RAID angegebenen Stripe zulässig sind.
Automatisierte RAID-Rekonstruktion
Einige RAID-Konfigurationen können von der Software im automatischen Modus erkannt und zusammengestellt werden. Wenn eine gute Komponente eines solchen RAID hinzugefügt wird, schlägt die Software vor, das RAID automatisch zu erstellen.
Bei Erfolg lädt die Software die RAID-Komponenten in der richtigen Reihenfolge und die gesamten RAID-Eigenschaften.
Bei einem Ausfall (z. B. bei einer Beschädigung der RAID-Konfiguration) können Sie die automatische RAID-Rekonstruktion abbrechen und das RAID manuell aufbauen.
Ergebnis
Im Falle einer erfolgreichen RAID-Rekonstruktion wird das Array als neuer Speicher im Navigationsbaum der Speicher hinzugefügt. Sie können alle für andere Speichertypen verfügbaren Vorgänge (einschließlich Hinzufügen von RAID als Komponente eines anderen RAID) auf dieses RAID anwenden.
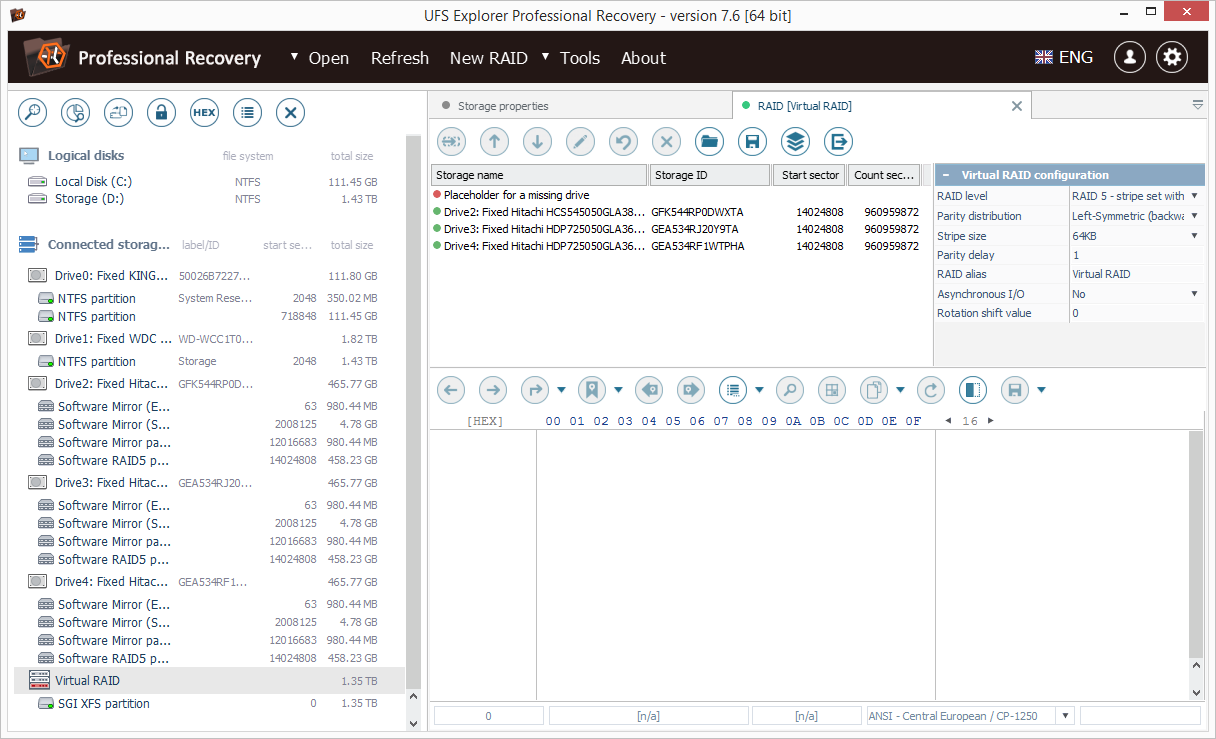
RAID speichern
Um eine RAID-Konfiguration zu speichern, wählen Sie sie im linken Navigationsbereich des UFS-Explorers in der Speicher-Navigationsstruktur aus und verwenden Sie die Kontextmenüoption "RAID-Konfiguration speichern". Sie können diese Konfiguration zukünftig über das Untermenü "Virtuelle Festplatte oder Image" des Hauptmenüpunkts "Öffnen" laden.
RAID-Konfiguration korrigieren
Um eine RAID-Konfiguration zu ändern, wählen Sie den benötigten virtuellen RAID-Speicher in der Navigationsstruktur von UFS Explorer aus und verwenden Sie die Kontextmenüoption "RAID-Konfiguration bearbeiten".
Dadurch wird eine Registerkarte "RAID Builder" mit vorkonfigurierten RAID-Komponenten und RAID-Parametern geöffnet. Wenn dieses RAID aufgebaut ist, ersetzt es das ursprüngliche RAID in der Navigationsstruktur der Speicher.
Das Tool ist nützlich zum Ändern (oder Erraten) von RAID-Parametern nach einer falschen Spezifikation.
Kompatibilität mit Runtime Software RAID-Konfigurationen
RAID-Konfigurationen im Format der Runtime-Software .vim-Dateien (Virtual Image-Dateien) werden von der Software unterstützt und können mithilfe des Untermenüs "Virtuelle Festplatte oder Festplattenabbild" des Elements "Öffnen" des Hauptmenüs importiert werden.
Zusätzlich implementiert SysDev Laboratories mehrere Erweiterungen des VIM-Dateiformats, die von Runtime Software-Produkten nicht unterstützt werden können:
Volle 64-Bit-Unterstützung für alle numerischen Parameter, einschließlich Offsets und Größen.
Unterstützung aller Image-Dateien und virtuellen Laufwerke (unterstützt vom UFS-Explorer) über .vim.
Unterstützung von .vim-Dateien unter Linux, macOS, BSD. Dies ändert das Format des Festplattenreferenzdatensatzes und hat das Format "HD $ {Pfad}", wobei $ {Pfad} der vollständige Pfad zu einem Blockgerät ist (z. B. HD / dev / sda :).
Benutzerdefinierte RAID-Konfigurationen
Um eine benutzerdefinierte RAID-Konfiguration anzuwenden, müssen Sie eine Textdatei (ASCII oder UTF-8 / UTF-16 mit Formatmarkierung) erstellen, die eine Anweisung für die RAID-Konfiguration enthält. RAID wird über den Befehl "stripes" konfiguriert, der die Argumente "stripe size" und "pattern length" verwendet. Der Befehlsblock beschreibt die Speicherkomponenten in ihrer Reihenfolge. Das "Komma" -Symbol begrenzt die Komponenten derselben Zeile; Das "Semikolon" beginnt mit der Beschreibung der nächsten Zeile. Ein optionales Argument für die Komponente definiert die Zeilenvoreingenommenheit der Komponente. Die Definition ist nicht Newline-sensitiv. Es ist erlaubt, Blockkommentare /*...*/ hinzuzufügen.
Um die erstellten Konfigurationsdateien zu laden, wählen Sie die Option "Benutzerdefinierter Datenverteilungsalgorithmus" aus der Dropdown-Liste neben dem Parameter RAID-Level im RAID-Eigenschaftenblatt aus und klicken Sie auf die Schaltfläche "Wert ändern" neben der Eigenschaft "Datenverteilungsalgorithmus". Nach dem erfolgreichen Import der Konfiguration zeigt die Software den Dialog zur Bestätigung der Konfiguration an.Wenn die Konfiguration korrekt ist, drücken Sie OK, um sie zu akzeptieren. Drücken Sie anschließend auf die Schaltfläche "Build" in der Registerkarte "RAID Builder", um die RAID-Assemblierung durchzuführen ein RAID-Speicher im UFS-Explorer.
Beispiel: RAID 5, linkssymmetrisch, 64-KB-Strip mit 4 Laufwerken ist definiert als: stripes (128,4) {
1,2,3;
4,1,2;
3,4,1;
2,3,4;
}
Ohne Zeilenumbrüche:
Streifen (128,4) {1,2,3; 4,1,2; 3,4,1; 2,3,4;}
Hier definiert "Streifen (128,4)" die Konfiguration mit der Streifengröße von 128 Sektoren und der Mustergröße von 4 Streifen. Die Aufzählung in {...} - Block definiert die Ordnungszahl der Komponenten. Semikolon definiert eine neue Musterzeile.
Mit dem Vorurteil können Sie dasselbe wie folgt schreiben: stripes (128,4) {1,2,3,4 (1), 1 (1), 2 (1), 3 (2), 4 (2), 1 (3), 2 (4), 3 (4), 4 (4)}
Anstelle einer Komponente können Sie auch einen funktionalen Ausdruck angeben. Zu den unterstützten Ausdrücken gehören "Rekonstruktion nach Parität", "Rekonstruktion nach Reed-Solomon-Code" oder "Kombination nach Parität und Reed-Solomon".
Die Formate von Funktionsausdrücken: Parität: P {1,2,3}. Hier: P - Paritätsfunktion, Aufzählungskomponenten zur Berechnung der Parität. Reed-Solomon: Q (5, g, 4) {1,2,3; 1,2; 3}. Hier: Q - Reed-Solomon-Code, 5 - Ordnungszahl der Platte, Position des Q-Stripe, g - Indextyp, 4 - Fehlender Laufwerksindex; Aufzählung - Datenträgernummern gefolgt von Datenträgerindizes (durch Semikolon getrennt), um den Reed-Solomon-Code zu berechnen.
a) Parität und Reed-Solomon: PQ (6,7, i, 4,5) {1,2,3; 1,2,3}. Hier: PQ - kombinierte Berechnung, 6 - P - Stripe - Laufwerksordnungsnummer, 7 - Q - Stripe - Laufwerksordnungsnummer, i - Indextyp, 4 - Plattenindex zum Rekonstruieren, 5 - Plattenindex des zweiten fehlenden Laufwerks; Enumeration - Datenträgernummern gefolgt von Datenträgerindizes (durch Semikolon getrennt), um den Reed-Solomon-Code zu berechnen. Indextyp g - bedeutet zwei Potenzwerte im Galois-Feld, i - nur ein einfacher Index.
Beispiele für RAID-Konfigurationen mit Rekonstruktion:
4 x RAID 5, linkssymmetrisch, 64-KB-Stripe, ohne Laufwerk 3:
a) Stripes (128,4) {
1,2, P {1,2,3};
3,1,2;
P {1,2,3}, 3,1;
2, P {1,2,3}, 3;
}
b) 5 x RAID 6, linkssymmetrisch, 64 KB Streifen ohne Laufwerk 3, Redundanzreihenfolge ist P, dann Q:
Streifen (128,5) {
1,2, P {1,2,3,4};
4,1,2;
3,4,1;
P {1,3,4}, 3,4;
2, P {2,3,4}, 3;
}
c) 5 x RAID 6, linkssymmetrisch, 64-KB-Streifen, ohne Laufwerke 3 und 5, Redundanz ist P, dann Q:
Streifen (128,5) {
1,2, P {1,2,3,4};
Q (3, g, 1) {1,2; 2,3}, 1,2;
3, P {1,2,3}, 1;
PQ {1,2, g, 1,3} {3; 2}, 3, PQ {1,2, g, 3,1} {3; 2};
2, Q (1, g, 2) {2,3; 1,3}, 3;
}
Wenn RAID eine "Paritätsverzögerung" hat, können Sie "Schleife" für die gesamte Spalte einschließlich funktionaler Ausdrücke mit der Funktion "repeat" angeben. Beispiel: 4 x RAID 5 Left Asymmetric, 16 KB Stripe-Größe und Paritätsverzögerung von 16 Stripes:
Stripes (32,64) {
repeat (16) {1,2,3};
Wiederholung (16) {1,2,4};
Wiederholung (16) {1,3,4};
Wiederholung (16) {2,3,4};
}
Platten angeben
Ein optionaler Abschnitt "Laufwerke". Wenn der Abschnitt nicht angegeben ist, verwendet RAID Builder die bereits definierten Komponenten. Wenn angegeben, ersetzt die Liste der Komponenten aus RDL die Liste in RAID Builder. Die unterstützten Komponententypen sind: "Festplatte" - ein physisches Laufwerk, "Image" - eine Festplatten-Image-Datei, "Span" - eine vordefinierte Komponentenspanne. Eine Komponente ist als Typ definiert (Identifikationsinformationen, Startoffset, Verwendungsgröße). Die Parameter "Startoffset" und "Größe verwenden" sind optional.
Beispiel:
Scheibe (1,2048,233432);
Bild (C: / image1.img,0,4096);
Bild (C: /image2.img);
Span (Myspan01,0,40960);
Informationen zur Identifizierung des physischen Laufwerks unter Windows sind die Ordnungszahl des Laufwerks. unter macOS, Linux usw. - der vollständige Pfad des Blockgeräts, für ein Disk-Image - der vollständige Pfad dieses Disk-Images, für Span - dessen Identifizierungsname.
Hier ein Beispiel für eine vollständige Konfiguration für HP RAID mit 4 x RAID 5 Left Asymmetric, 16 KB Stripe-Größe und Paritätsverzögerung von 16 Stripes:
Laufwerke {
Festplatte (1,1088);
Scheibe (2,1088);
Scheibe (3,1088);
Scheibe (4,1088);
}
Streifen (32,64) {
Wiederholung (16) {1,2,3};
Wiederholung (16) {1,2,4};
Wiederholung (16) {1,3,4};
Wiederholung (16) {2,3,4};
}
Wenn eine Konfiguration nur den Abschnitt "Laufwerke" enthält, werden die Komponenten einfach in RAID Builder geladen, ohne eine RAID-Konfiguration zu definieren.
Spannweite definieren
Eine Spanne kann mit Hilfe des Abschnitts "Defspan" definiert werden. Es muss definiert werden, bevor es als Komponente verwendet werden kann. Die Definition der Span-Definition lautet: defspan (name) {enumeration}. Die Aufzählung kann die gleichen Komponenten enthalten wie für den Abschnitt "Laufwerke" (einschließlich Spannweiten).
Beispiel:
defspan ("myspan01") {
disk (1,2048,233432);
Bild ("C: /image1.img", 0,4096);
Bild ("C: /image2.img");
span ("myspan00", 0,40960);
}
Mit RDL kann ein einfacher Span mit folgendem Code geladen werden:
defspan ("images") {
image ("C: /image1.img");
Bild ("C: /image2.img");
Bild ("C: /image3.img");
}
Laufwerke {
span ("Bilder");
}
Streifen (1,1) {1}
3.3.7 Datenänderung
Die Software ermöglicht die Datenänderung direkt auf den Quelllaufwerken zur Korrektur logischer Datenstrukturfehler. Dies beinhaltet jedoch auch das Risiko eines dauerhaften Datenverlusts. Bevor Sie die Datenänderungs-Tools verwenden, sollten Sie daher absolut sicher sein, was Sie tun. Es wird außerdem dringend empfohlen, eine Sicherungskopie des Quellspeichers zu speichern und mit dieser Kopie zu arbeiten.
Die Bearbeitungsfunktionen stehen für Festplatten (einschließlich Festplattenimages und virtuelle Festplatten) zur Verfügung, nicht jedoch für RAID oder Dateien.
Um den "Bearbeitungsmodus" zu aktivieren, klicken Sie im Bereich "Hexadezimal-Viewer" auf die Schaltfläche "Daten ändern" oder verwenden Sie die Kontextmenüoption "Inhalt bearbeiten". Dadurch wird eine neue Registerkarte "Hexadezimal-Editor" geöffnet, die mit einem roten Symbol gekennzeichnet ist. Wenn der Hexadezimal-Editor vom Hexadezimal-Viewer aufgerufen wird, wird er auf dieselbe Speicheransichtsposition konfiguriert. Der Hexadezimal-Editor unterstützt alle Funktionen des Hexadezimal-Viewers und wird mit Datenmodifikationstools im unteren Bereich erweitert. Der Hexadezimal-Editor akzeptiert auch Datenänderungen über die Tastatur oder das Kopieren von Daten mithilfe der Zwischenablage.
Sie können den Speicherinhalt sowohl mit rohen Zwischenablage-Daten einfügen (überschreiben) als auch den Inhalt der Zwischenablage als Hexadezimal-Text (über das Werkzeug "Einfügen als") analysieren.
Schließlich gibt es Werkzeuge, um Datenbereiche auszufüllen oder komplexere Byte-Transformationen durchzuführen.
Wenn die Anzahl der Änderungen die Rückgängigmachungsgrenze nicht überschreitet, werden alle Änderungen vor einem expliziten "Speichern" -Befehl im Speicher ausgeführt und können rückgängig gemacht werden. Wenn zu viele Änderungen vorgenommen wurden, werden Sie aufgefordert, die Daten zu speichern, um fortfahren zu können. Wenn für einen einzelnen Vorgang zu viel Speicherplatz für den Undo-Puffer erforderlich ist, kann der Vorgang direkt im Speicher ausgeführt werden, ohne dass die Möglichkeit besteht, ihn rückgängig zu machen.
Beispiel: Um alle Daten auf einer Festplattenpartition zu löschen, öffnen Sie diese zum Schreiben (Kontextmenüoption "Inhalt ändern"). Dadurch wird der Hexadezimal-Editor geöffnet. Überprüfen Sie die Daten, um sicherzustellen, dass die richtige Partition ausgewählt ist. Wählen Sie alle Daten mit der Tastenkombination "Strg + A" aus. Drücken Sie die Taste "Auswahl ändern". Wenden Sie die Aktion "Bytes ersetzen" mit 0 an (Standardaktion). Warten Sie auf den Abschluss.
3.3.8 Erstellen von "Klonen" von Festplatten, virtuellen Festplatten, RAID usw.
Die Software ermöglicht das Erstellen einer Bit-zu-Bit-Kopie eines unterstützten Speichers auf einer Festplatte.
Um dies zu tun:
- Stellen Sie sicher, dass alle Registerkarten geschlossen sind, um eine falsche Auswahl zu vermeiden.
- Öffnen Sie den Quellspeicher im Hexadecimal Viewer und prüfen Sie dessen Inhalt.
- Öffnen Sie den Zielspeicher zum Schreiben (die Kontextmenüoption "Inhalt ändern") und stellen Sie sicher, dass keine wertvollen Daten vorhanden sind.
- Wählen Sie im Hexadezimal-Editor für den Zielspeicher "Daten mit ... überschreiben".
- Im Dialog wählen Sie den Quellspeicher, seine Startposition und die Anzahl der zu übertragenden Sektoren.
- Starten Sie den Prozess und warten Sie auf seinen Abschluss.
Die Aktion kann nicht rückgängig gemacht werden.
4. Rechtliche Hinweise
4.1 Urheberrecht
UFS Explorer-Produkte werden lizenziert, nicht verkauft. Dies bedeutet, dass Ihnen der rechtliche Eigentümer der Software (SysDev Laboratories LLC) nur einige Rechte für die Verwendung der Software gewährt. Bitte lesen Sie die Endbenutzer-Lizenzvereinbarung, um weitere Informationen zur Softwarelizenzierung zu erhalten.
Die Endbenutzer-Lizenzvereinbarung ist eine öffentliche Angebotsvereinbarung. Jede Verwendung der Software (einschließlich Kopieren, Installation, Verwertung usw.) bedeutet, dass Sie den öffentlichen Angebotsvertrag akzeptiert haben. Ab dem Zeitpunkt der Annahme tritt das Abkommen in den meisten Ländern der Welt in Kraft.
Nur SysDev Laboratories LLC, der Autor der Software und autorisierte Wiederverkäufer sind berechtigt, Registrierungscodes für Anwendungen herauszugeben, die Eigentum von SysDev Laboratories LLC sind. Die unberechtigte Verwendung eines Registrierungscodes verstößt gegen ukrainische und internationale Urheberrechtsgesetze.
Jede Veröffentlichung eines Registrierungscodes durch einen Lizenzinhaber oder eine unerlaubte Übertragung der Lizenz führt zur Kündigung des Endbenutzer-Lizenzvertrags.
Der Endbenutzer-Lizenzvertrag ist ein öffentlicher Kaufvertrag, der in der Ukraine und in anderen Ländern rechtlich gültig ist. Durch die Installation und Verwendung der Software akzeptieren Sie dieses öffentliche Angebot. Die Verletzung des EULA kann in diesen Ländern als Straftat betrachtet werden.
4.2 Lizenzinformationen
UFS Explorer Professional Recovery wird auf Basis der folgenden Lizenzen verkauft:
- Test- / Evaluierungslizenz - Die Software kann nur von Einzelpersonen zu Evaluierungszwecken verwendet werden. Ein Lizenzinhaber muss den "Testeinschränkungen" der Software zustimmen.
- Unternehmenslizenz - Die Lizenz gilt für Software, die von einer juristischen Person, einem Unternehmen oder einer Organisation auf bis zu zehn (zehn) Computern verwendet wird, die sich im Eigentum eines Lizenzinhabers befinden und nicht zu Gewinnzwecken eingesetzt werden. Ein Lizenzinhaber ist nicht berechtigt, "gewinnorientierte" Dienste mit der Software zu erbringen oder zu Hause für persönliche Zwecke zu nutzen. Die Software kann nicht auf Computern von Drittanbietern (z. B. Kunden eines Lizenzinhabers) installiert werden.
- Kommerzielle Lizenz - Die Lizenz gilt für Software, die von einer juristischen Person, einem Unternehmen oder einer Organisation auf einem Computer verwendet wird, der einem Lizenzinhaber zu kommerziellen Zwecken gehört. Die Software kann nicht auf Computern von Drittanbietern (z. B. Kunden eines Lizenzinhabers) installiert werden.
Die Corporate- und Commercial-Lizenzen erfordern die Zahlung der Lizenzgebühr. Nach dem Kauf einer Softwarelizenz autorisiert SysDev Laboratories diese mit der Herausgabe eines Software-Registrierungscodes. Dieser Code wird verwendet, um die Programmfunktionen freizuschalten ("Testeinschränkungen entfernen") und einen Lizenzinhaber als berechtigten Besitzer der Software zu identifizieren.
Ein Registrierungscode für eine Unternehmens- oder kommerzielle Lizenz wird auf den Namen des Unternehmens oder den Namen der Person (Unternehmer) ausgestellt und ermächtigt die Person / Firma, die Anwendung gemäß den Bestimmungen des EULA zu verwenden.
4.3 Kontakte
Firmendetails
Hauptbüro:
Gesellschaft mit beschränkter Haftung SysDev Laboratories
Code der juristischen Person: 35951055
28-W Druzhby Narodiw Blvd,
Kiew, 01103, Ukraine
E-Mail: info@sysdevlabs.com
Um unser Support-Team zu kontaktieren, füllen Sie bitte das Kontaktformular aus.
5. Glossar
In diesem Abschnitt werden die wichtigsten Begriffe und Begriffe beschrieben, die erforderlich sind, um die Besonderheiten der Arbeit mit der Software zu verstehen.
5.1 RAID
RAID (Redundant Array of Independent Disks) ist eine spezielle Technologie für die Datenspeicherorganisation, bei der mehrere separate Festplatten zu einem einzigen System zusammengefasst werden. In einem solchen System werden die Daten im Gegensatz zu herkömmlichen linearen Speichern auf eine typische RAID-Ebene über die Laufwerke verteilt. Jede Ebene hat ihre Vor- und Nachteile, aber die Hauptidee eines RAID ist ein Gleichgewicht zwischen maximaler Leistung, erhöhter Zuverlässigkeit und voller Kapazität an nutzbarem Speicherplatz.
Ein Betriebssystem erkennt RAID als einzelnes Laufwerk, das ihm einen eigenen Mountpunkt gibt und alle Festplatten als einen einzigen Speicher behandelt. Ein RAID-Controller ist für den korrekten Betrieb des Systems verantwortlich, das entweder hardwaremäßig oder softwarebasiert sein kann.
Zu den am häufigsten verwendeten RAID-Stufen gehören:
- JBOD ist nicht exakt RAID, da es keine Redundanz oder erhöhte Fehlertoleranz aufweist. Im Allgemeinen ist dies nur eine Reihe von Datenträgern (nicht notwendigerweise von derselben Größe), die zum Speichern von Daten kombiniert werden, da die Datenträger nacheinander gefüllt werden. Diese Technik wird auch als Disk Spanning bezeichnet.
- RAID0 basiert auf Daten-Striping ohne Redundanz. Jede Platte im System ist in separate Segmente - Streifen unterteilt. Während des Schreibvorgangs werden die Daten in Stücke geschnitten, die der Streifengröße entsprechen, und nehmen gleichzeitig die Plattenstreifen auf: Während ein Datenteil noch geschrieben wird, beginnt das System die Eingabe des nächsten. Im Allgemeinen ist RAID0 die schnellste Konfiguration in Bezug auf Eingabe / Ausgabe, jedoch die am wenigsten fehlertolerante. Wenn eine Platte eines solchen Systems ausfällt, werden die Daten des gesamten Systems unlesbar.
- RAID 1 wendet die Spiegelungsmethode an. Während des Schreibvorgangs erstellt das System eine exakte Kopie der Daten auf einem anderen Laufwerk. Wenn eine Platte ausfällt, bleibt die andere Platte lesbar. Diese Methode bietet jedoch die höchste Zuverlässigkeit und die umfangreichste Festplattenkapazität. Festplatten arbeiten nur paarweise: Das System funktioniert nicht mehr vollständig, ohne dass alle Laufwerke in Betrieb sind. RAID 1 ist die perfekte Wahl für Situationen, in denen das Sichern von Daten von entscheidender Bedeutung ist.
- RAID 3 ist das erste RAID-Level, das Parität verwendet. In Kombination mit dem Daten-Striping wie bei RAID0 verfügt dieses System über eine separate dedizierte Festplatte, auf der die Parität für andere Festplatten gespeichert wird. Aufgrund des Schreibens auf Byte-Ebene und einer separaten Festplatte, auf der die Parität berechnet und geschrieben wird, kann RAID 3 keine hohe Geschwindigkeit aufweisen. Ein solches System gewährleistet die Systemsicherheit auf Kosten eines langsamen Betriebs. Aus diesem Grund ist RAID 3 nicht sehr beliebt. Im Fehlerfall werden Daten mit Hilfe der intakten Datenträger und der Parität abgerufen.
- RAID 4 verwendet dasselbe Modell wie RAID 3 (dh Striping mit dedizierter Parität), mit einem Unterschied: Während RAID 3 auf Byteebene arbeitet, verarbeitet dieses Daten auf Sektorebene. Dadurch wird das Schreibproblem in gewissem Maße gelöst. Dennoch hat RAID 5, eine schnellere und zuverlässigere Konfiguration, RAID4 ersetzt. Wie bei RAID 3 wird dieses Level mit Hilfe der verbleibenden Festplatten plus der Festplatte mit Parität wiederhergestellt.
- RAID 5 basiert auf dem Prinzip des grundlegenden Datenstreifens, ähnlich wie bei RAID0, und der Redundanz von RAID 3, gilt jedoch als fortschrittlichere Technologie als seine Vorgänger. In RAID 5 werden Paritätsinformationen nicht auf einer separaten Festplatte gespeichert, sondern gemäß speziellen Rotationsverfahren auf alle Datenplatten verteilt. Diese Methode hat das Schreiben beschleunigt, da das System nicht warten muss, bis die Parität auf einer separaten Platte berechnet wird. Wenn eines der Laufwerke ausfällt, werden die Daten von den verbleibenden Laufwerken mit Hilfe von Parity abgerufen.
- RAID 6 ist ein weiterer Schritt auf dem Weg zu höherer Zuverlässigkeit. Diese Methode beinhaltet zwei Paritätsebenen, die auf alle Festplatten verteilt sind, und zwar nach speziellen Reihenfolge- und Rotationsschemata. Im Vergleich zu anderen Stufen ermöglicht RAID 6 die Datenwiederherstellung bei zwei fehlenden Laufwerken. Dieses Schema ist das zuverlässigste, aber das kostengünstigste, da ein zusätzliches Laufwerk zum Speichern der Parität verwendet wird.
6. Anhang
In diesem Abschnitt werden die häufigsten Fragen der Benutzer beantwortet. Für weitere Informationen wenden Sie sich bitte direkt an die Entwickler der Software über das Kontaktformular.
Ändert die Software die Daten auf den Quelllaufwerken?
Quelllaufwerke werden im schreibgeschützten Modus geöffnet, sodass die Software die Daten nicht ändern kann. Diese Software-Edition enthält jedoch Werkzeuge zur expliziten Datenänderung. Jede falsche Verwendung des letzteren kann zu einem dauerhaften Datenverlust führen.
Welches Dateisystem wird auf meinem Speicher angewendet?
Wenn ein Dateisystem von UFS Explorer unterstützt wird, wird es in der Speicher-Navigationsstruktur als Partition mit einem bestimmten Namen angezeigt. Für "NTFS-Partition" ist beispielsweise "NTFS" der Dateisystemtyp.
Unterstützt es ein X-Dateisystem?
Diese Informationen sind in den Softwarespezifikationen enthalten. Dies kann jedoch durch Ausführen einer Testversion der Software überprüft werden.
Wie kann man eine Partition im UFS Explorer identifizieren?
Suchen Sie das Laufwerk und das Dateisystem der entsprechenden Größe. Sie können jedoch das Dateisystem im Explorer öffnen und die darin enthaltenen Dateien überprüfen.
Meine dynamische Windows-Festplatte wurde von der Software nicht erkannt. Worin besteht das Problem?
Die Software hat wahrscheinlich ein komplexes dynamisches Laufwerk definiert (z. B. Span, Stripe, RAID 5 usw.). Der UFS-Explorer stellt RAID nicht automatisch zusammen. Wenn ein solches RAID von Windows als Volume bereitgestellt wird, können Sie es als "Speichergerät" öffnen, indem Sie seinen Einhängepunkt (NTFS-Pfad oder Laufwerkbuchstabe, gefolgt von einem Doppelpunkt) angeben.
Daten, die auf einem Software / Hardware-basierten RAID gespeichert sind, werden vom Betriebssystem nicht erkannt. Wie kann ich auf die Daten zugreifen?
UFS Explorer Professional Recovery unterstützt die Rekonstruktion von virtuellen RAIDs und verwendet ein solches RAID als virtuellen Speicher für den Zugriff auf die Daten.
Die Disk-Image-Datei ist in viele Fragmente aufgeteilt. Wie kann man auf die Daten zugreifen?
Das gesamte Festplatten-Image kann mithilfe der Hauptmenüoption "Festplatten-Image von Chunk-Dateien" aus Fragmenten kombiniert werden.
Es gibt schlechte Cluster. Wie können die Daten gelesen werden?
Wenn die Daten wertvoll sind, wenden Sie sich zur Datenwiederherstellung an ein Datenwiederherstellungsdienstlabor. Wenn die Daten weniger kosten als die Gebühr für einen Datenwiederherstellungsdienst, können Sie die Software verwenden, um eine Datenwiederherstellung zu versuchen.
Bei Dateisystemfehlern wird empfohlen, die Dateisystemrekonstruktionswerkzeuge von UFS Explorer zu verwenden.
Mein externes Laufwerk wurde nicht erkannt. Welche Schritte sollte ich unternehmen?
A: Überprüfen Sie den Verbindungstyp des Datenkabels und ob ausreichend externe Stromversorgung für das Laufwerk vorhanden ist (z. B. können 3,5-Zoll-Laufwerke nicht über USB mit Strom versorgt werden). Stellen Sie sicher, dass das Betriebssystem das Laufwerk als Gerät erkennt, damit die Software das Laufwerk erkennt.
In Windows: Klicken Sie mit der rechten Maustaste auf "Computer" und wählen Sie "Verwalten". Gehen Sie zu "Speicher" und "Datenträgerverwaltung". Stellen Sie sicher, dass der Datenträger aufgelistet ist.
In Linux und MacOS gibt es im Bereich "Systemanwendungen" "Disk Utility", das zu den gleichen Zwecken verwendet werden kann.
Wichtig: Wenn Sie eine Festplatte eines anderen Betriebssystems an einen Computer mit Windows-Betriebssystem angeschlossen haben, werden Sie möglicherweise nach der Aktivierung der Festplatte gefragt. Lehnen Sie diese Aufforderung ab, um Datenverlust zu vermeiden.
Das Betriebssystem erkennt die Festplatte, UFS Explorer dies nicht. Was soll ich als nächstes tun?
Stellen Sie sicher, dass die Software mit einem lokalen Administrator-Benutzerkonto ausgeführt wird (dies ist für den Zugriff auf physische Laufwerke erforderlich).
Wenn andere Festplatten (außer der erforderlichen) erkannt werden, kann dies auf einen fehlerhaften Cluster im Sektor 0 des Laufwerks hindeuten. In diesem Fall kann auf die Festplatte noch über "Read-It-Once" zugegriffen werden.
7. Tastenkombinationen
Die folgenden Tastenkombinationen funktionieren auf der Registerkarte Hexadezimal-Inhalt.
+ Rücktaste
+ Umschalt + =
+ Umschalttaste + A
+ Umschalttaste + C
+ Umschalttaste + K
+ Umschalttaste + P
+ Umschalt + R
+ Umschalttaste + S
+ Umschalt + T
+ Umschalttaste + U
+ Umschalttaste + V

