Can I recover data from an encrypted storage?

It is probably not a secret that the modern word almost fully relies on digital technologies. This makes security of sensitive information a matter of increased concern. Not only businesses and institutions but also home users are becoming ever more vigilant when it comes to protection of valuable data. Сustomer information, company secrets, intellectual property items, accountancy or any personal data, like identity, health and financial information are vulnerable to cyber attacks, especially when simply left as they are. In view of this, more and more people are deploying encryption tools on their storage devices. They perform mathematical calculations to encode the data and ensure its non-readability for any unauthorized person. At the same time, such files remain unprotected from failures or damages within the system, let alone the data loss risks derived from the implementation of this technology. There is even a common belief that encrypted data cannot be restored. But in fact, though encryption adds complexity to the recovery process, in most cases, it doesn’t prevent it entirely.
Encryption tools transform data into cipher-text which can be unlocked only with decryption credentials, usually a password or a unique sequence of symbols referred to as a decryption key. The unavailability of this information makes it impossible to decrypt the drive neither by the authorized user nor by a data recovery utility. In addition, each of them allocates a certain area on the disk to special metadata required for the decryption procedure. Although its location and content vary for different encryption products, if it gets corrupted or overwritten, no software will be able to translate the ciphered data back to its original form.
If you have the right password/decryption key and the critical metadata wasn’t severely damaged, as a rule, there are quite high chances to salvage files from an encrypted disk. However, there are still several points to keep in mind:
- If the drive has bad sectors, it is highly recommended to clone it and work with the disk image instead of a physical device. The matter is that their number has a potential to increase during the operation of the device and one cannot predict which part of the disk they will occupy and whether it will contain some crucial decryption metadata. The same applies to high-capacity disks with low performance – the drive may be unable to withstand the workload and fail during the procedure.
Warning: Please familiarize yourself with the peculiarities of the imaging process for defective disks.
- If you are not certain that you have the right decryption password/key, don’t try to decrypt the drive in your operating system, as it may get locked after multiple attempts to use the wrong one. Instead, employ the decryption techniques provided by data recovery software, which appeals to the physical device and emulates its operation, making it possible to guess the password by process of elimination.
- Overwriting operations performed by the system, user, file shredding utilities or the TRIM command on SSDs render any deleted data irrecoverable, no matter whether it is encrypted or not.
- If encryption was activated on the system startup drive in macOS 10.13 High Sierra and later, in order to enable data recovery from it, you will need to disable System Integrity Protection as demonstrated in Unblocking access to macOS drives. Also, please note that the procedure is not possible for internal drives on Macs that rely on custom Apple’s M1 (Apple Silicon) or T2 security chips.
- Before trying to decrypt and restore data by yourself, ensure the health of your drive. If you suspect any problems, contact a reliable data recovery center.
Recover files from a disk encrypted with BitLocker, LUKS, TrueCrypt, VeraCrypt, FileVault 2 or APFS encryption
If the data was lost from your encrypted disk after some sort of logical failure, for instance, due to an unexpected system shutdown, OS crash or accidental deletion, but you still have at least one of the defense elements provided by your encryption utility (password, recovery key, key file, etc.), the right data recovery tool can easily bring the missing files back. SysDev Laboratories has conducted extensive research in this field studying the technology behind different encryption utilities and implemented these findings in the UFS Explorer and Recovery Explorer software solutions. The programs employ efficient decryption techniques for most popular methods of encryption, such as BitLocker, LUKS (both LUKS1 and LUKS2), TrueCrypt, VeraCrypt, FileVault 2 and APFS encryption, enabling the user to unlock the storage and recover data from it like from any non-encrypted device.
In order to restore your files from an encrypted volume with the help of UFS Explorer Professional Recovery, take the following steps:
-
Download and install the application onto the computer. Its operating system has to match the version of the program.
Hint: If you have any difficulties with the installation of the utility, please refer to the installation manual for UFS Explorer Professional Recovery.
-
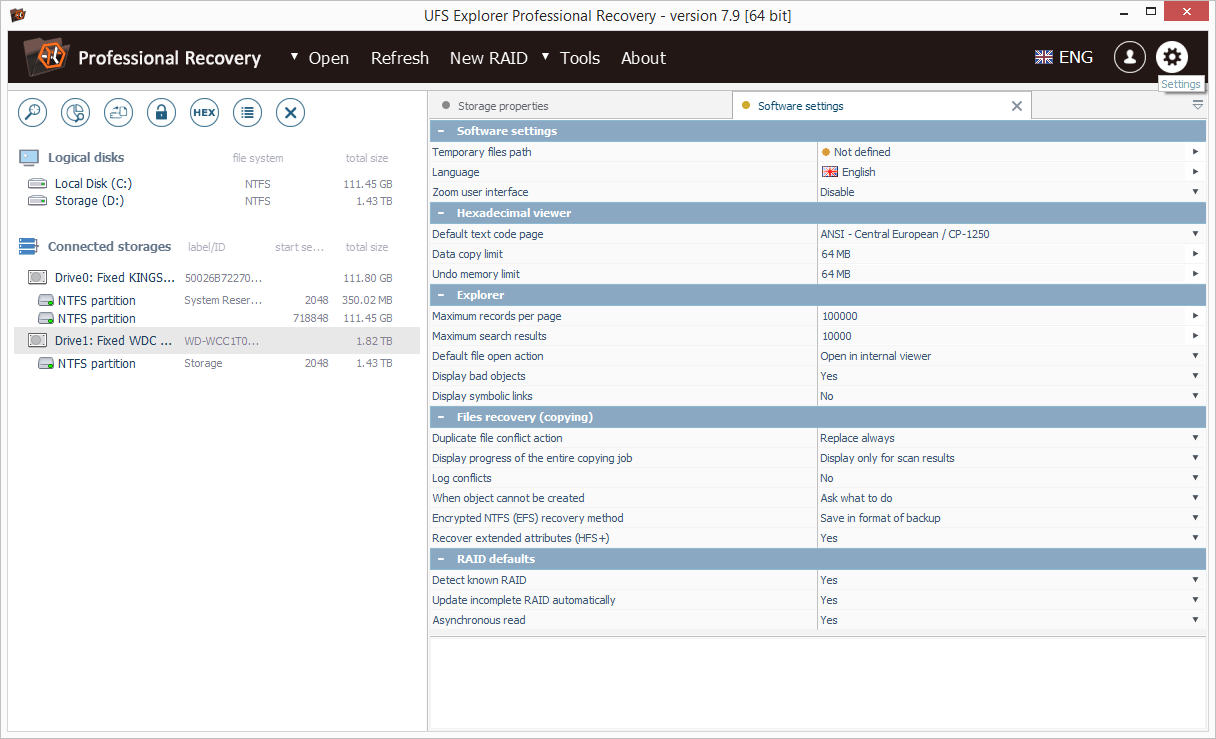
Launch the software and, if needed, change its parameters in the corresponding tab.
-
Connect your encrypted device to the machine. If possible, use the fastest available interface.
Hint: If you need to attach an internal hard drive from another computer, you can plug the disk into the motherboard of your PC or сonnect the drive externally using a USB to SATA/IDE adapter.
-
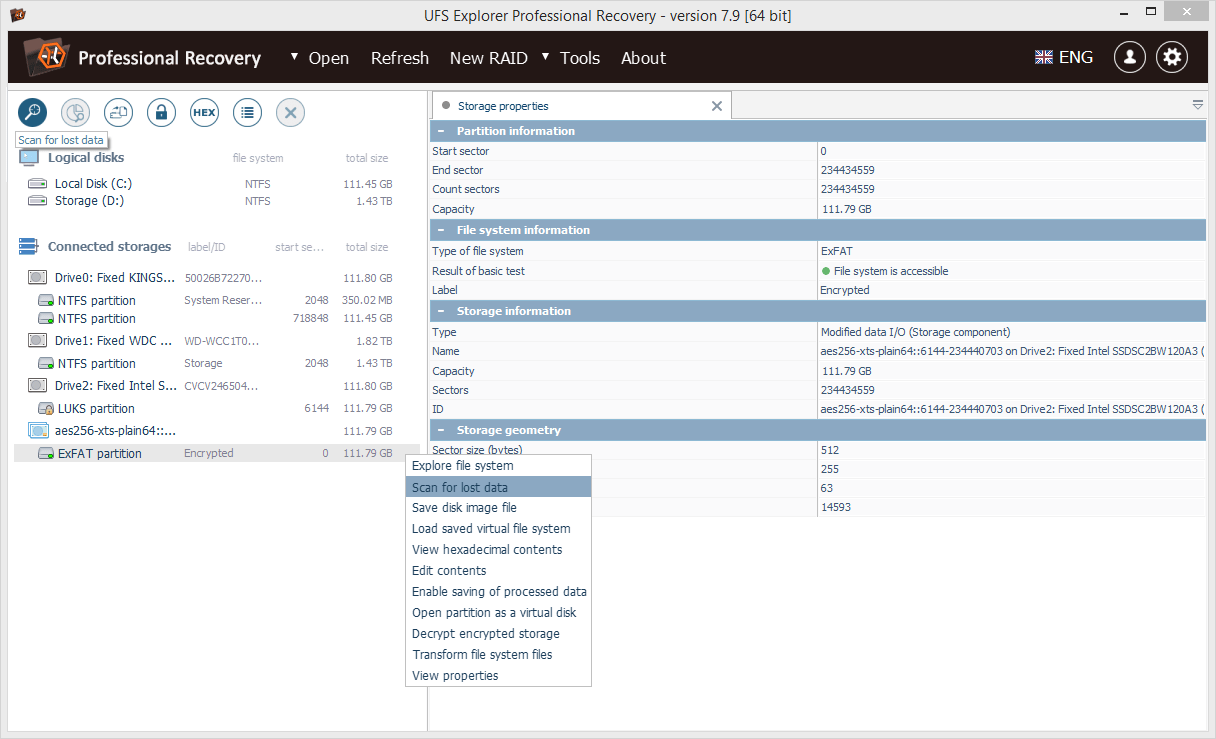
Find your encrypted drive/volume among the options under connected storages in the left pane of the main screen. It can usually be identified by the yellow padlock icon. In our case, a volume encrypted with LUKS is used as an example. Open its context menu and select the "Decrypt encrypted storage option".
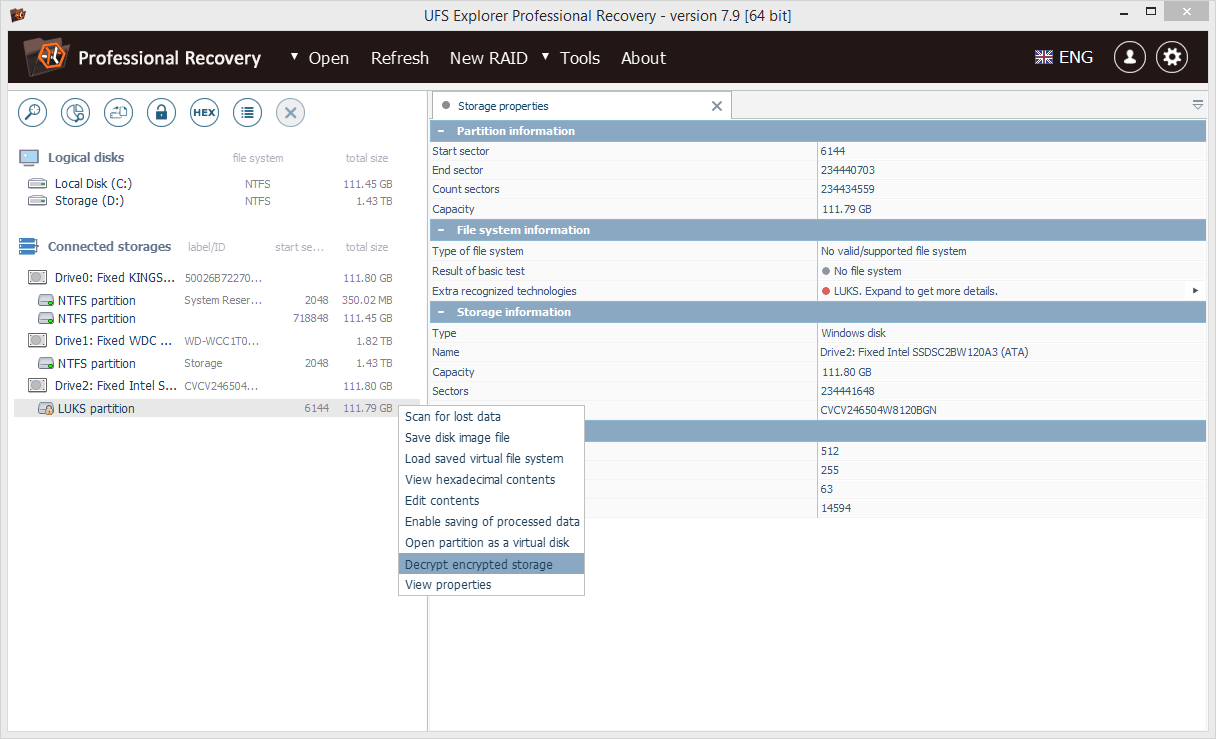
Note: If you are dealing with an HFS+ partition encrypted with FileVault 2, choose the "Open as Apple Core Storage volume" from the context menu instead.
Hint: If you want to learn more about how different drives and volumes are labeled in the interface of UFS Explorer, please refer to Identification of different storages and technologies.
-
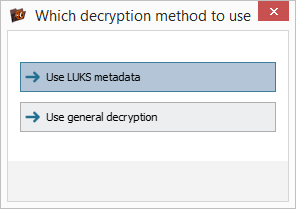
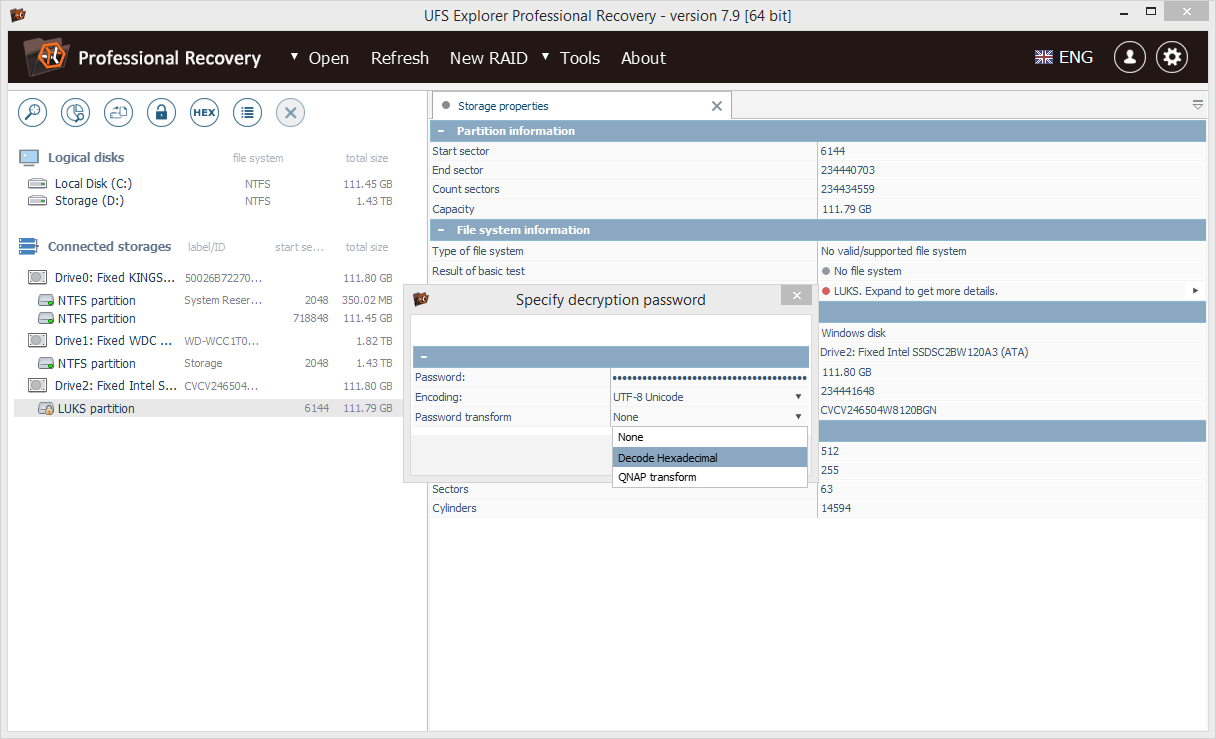
Choose the decryption method which corresponds to the applied encryption technology and specify the correct user password or copy the recovery key from its file and paste it into the field.
If the password for some reason contains unprintable symbols, it must be specified as hexadecimal code and "Password transform" must be enabled as "Decode Hexadecimal".
-
Select the decrypted volume mounted by the program (in our case, it is an exFAT partition) and scan it for lost data with the help of the respective button or the storage context menu option.
Hint: To learn more about file systems and their types, please, refer to the basics of file systems.
-
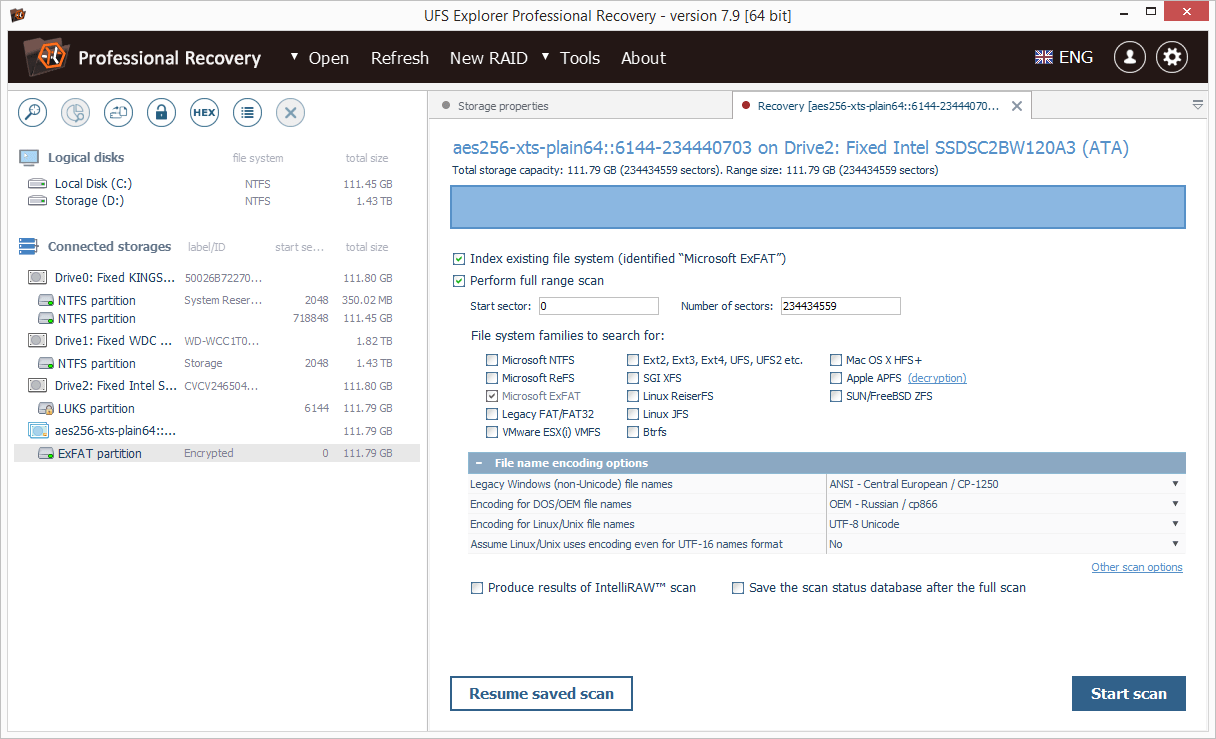
Provide the desired scan parameters. If you are sure concerning the file system type, deselect the rest of the file systems. After that, press "Start scan" and wait for the process to complete.
Hint: If you need help with setting up the scanning procedure, please, refer to the instruction on performing a storage scan.
-
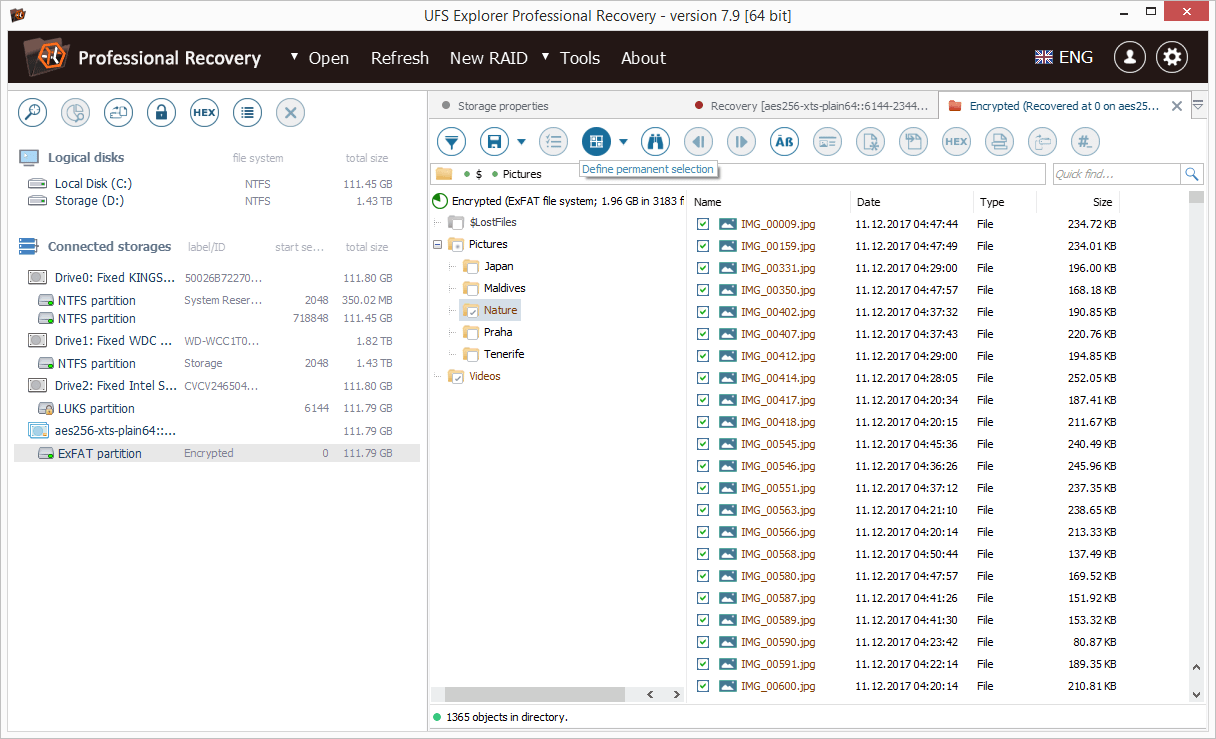
Explore the presented file system result: you may sort the files by name, date, type, utilize quick or advanced search and preview images, videos, audio files or PDF documents. After that, press "Define permanent selection" and choose the items you would like to copy by putting checkmarks right next to them.
Hint: The information provided in Evaluation and saving the results of data recovery may facilitate your work with the obtained folders and files.
-
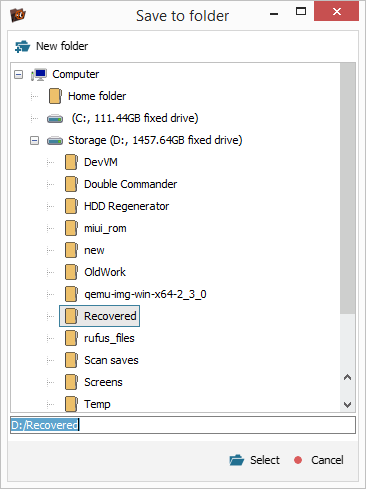
Press "Save selection" and choose a destination folder for these files in the pop-up window. Make sure you are saving them to a logical disk other than the one from which they are being recovered.
Hint: The overall process is also demonstrated in the video tutorials dedicated to data recovery from LUKS, BitLocker and APFS-encrypted volumes.
Last update: August 09, 2022
